Want to join in? Respond to our weekly writing prompts, open to everyone.
from Unvarnished diary of a lill Japanese mouse
JOURNAL 10 juin 2026
Pour le moment je vois pas trop la lumière au bout du chemin. On mène une vie qui nous plaît pas. C’est tout à fait, en un peu mieux, la vie japonaise standard : boulot dodo boulot. On est privilégiées, on a des moments libres que beaucoup n'ont pas, mais ils nous servent surtout à voir notre aliénation le reste du temps.
Bien sur on fait des choses qui nous plaisent, d'accord, mais c'est pas ce qu'on aimerait en vrai. On veut pas attendre d'être vieilles, c’est trop triste, notre jeunesse s'évapore. Bientôt il ne restera rien, le bol sera vide on sera sèches.
Ah ! encore un an avant que ma chérie puisse demander la nationalité japonaise, faut être patientes. Mais quand même, attendre toujours attendre, le temps passe c’est comme un train, si tu montes pas dedans, il part sans toi.
The Companions Placed Along the Road
from Wayfarer's Quill
There are travelers we choose, and travelers we don’t. Yet the longer I walk this winding road, the more I suspect that choice was never the point.
In an older Sunday sermon, Bishop Barron reflected on a simple but unsettling truth: we don’t always get to choose the people we’re called to love. Some arrive like sunlight — easy, warm, familiar. Others enter our lives like weather we didn’t prepare for, testing the seams of our patience and the sturdiness of our compassion.
But what if every person who crosses our path is placed there with intention?
What if each encounter, whether that be pleasant or difficult, is a quiet invitation from God to grow?
Some companions teach us joy. Others teach us endurance. A few teach us forgiveness in ways we would never have chosen. Yet all of them, in their own way, shape the soul of the traveler we are becoming.
So the call is simple, though never easy: Don’t only love the ones who are easy to love. Love the ones you’re given.
For in the great pilgrimage of life, even the difficult companions may be the very ones who carve out deeper wells of grace within us.
#Reflection #BishopBarron #GraceInTheEveryday
The Silence Beside the Workbench
from Douglas Vandergraph
Chapter One
Jesus knelt before dawn with His hands resting open upon His knees, the packed earth cool beneath Him and the house still around Him. Outside, Nazareth had not yet become noise. A rooster called somewhere down the slope, then another answered from farther away, and the dark blue of morning held the village in that brief mercy before burdens remembered their owners. Jesus did not hurry His prayer. He was ten years old, small enough that the world still looked over Him, yet there was a stillness in Him older than the stones around the well. He breathed in the quiet, and in that quiet He listened to His Father as if nothing in heaven or earth was more natural than a boy kneeling before the day began.
Mary had risen but had not disturbed Him. She moved carefully near the hearth, setting a little grain aside, tending the small fire in a way that made almost no sound. Joseph’s tools lay against the wall, wrapped in their usual order, waiting for the work that would soon fill the morning. A shaved piece of cedar rested near the doorway where Joseph had left it the night before, its clean scent faint in the air. Jesus remained bowed. He prayed for His mother’s strength, for Joseph’s hands, for the village waking under its ordinary troubles, and for one house near the edge of the lane where a lamp had burned too late. Anyone searching for Jesus of Nazareth age 10 story might imagine wonder first, but the wonder of that morning was quiet enough to be missed by anyone in a hurry.
When He rose, He did not speak at once. He stepped outside and looked toward the narrow path where the neighbor’s courtyard opened behind a leaning wall. In that house lived Eliab, a boy nearly twelve, though grief had made him carry himself like someone much older. Eliab’s father had died the year before after a fever that had passed through Nazareth and taken three men before the figs were ripe. Since then, Eliab had learned how to lower his eyes before pity could reach him. He had learned how to answer quickly when adults asked if he was well. He had learned how to be useful so no one would notice how afraid he was. In a quiet companion reflection on young Jesus in Nazareth, the village might have seemed gentle from a distance, but inside its small rooms people still hid the things they did not know how to name.
Joseph came to the doorway with a leather strap in one hand and a patient look on his face. He watched Jesus watching the lane. “You are thinking of Eliab.”
Jesus turned toward him. “His mother’s lamp was still burning when the moon crossed the ridge.”
Joseph’s face softened, though the line between his brows deepened. “Mara is taking in more mending than her eyes can bear. Eliab brought a cracked yoke piece yesterday and asked if I would let him sweep the shop floor to pay for the repair. I told him the repair was small, but he kept standing there as if kindness were a debt he could not carry.”
Mary came near enough to hear. She wiped her hands on her outer garment and looked toward the same lane. “His mother asked for no help when I saw her at the well. That is not the same as needing none.”
Jesus looked down at His hands. They were still the hands of a child, but they had already learned the shape of wood, the weight of water, the roughness of rope, and the tenderness required when touching something cracked. “May I go to him after morning work?”
Joseph nodded slowly. “You may. But do not press where a wound is guarded. Some doors open only when a person is no longer afraid of what will be seen inside.”
Jesus received the words with the seriousness of prayer. Then He helped Mary with the water jar and carried kindling to the hearth before the sun cleared the rooftops. The day began as most days did, not with great events but with the steady demands that keep a household alive. Joseph took Him to the work place beside the house, where the first light reached the shavings on the ground and made them look almost golden. A farmer from Cana had sent word about a plow beam needing attention, and Joseph examined the wood with care, letting Jesus run His fingers along the split.
“Tell me what you feel,” Joseph said.
Jesus touched the grain gently. “It did not break all at once. It was strained for a long time before it opened.”
Joseph looked at Him for a moment, then back at the beam. “Yes. Many things are like that.”
Jesus did not answer, but His eyes went again toward Eliab’s house.
By the time the village fully woke, women were moving toward the well with jars balanced against hip or shoulder, men were calling to animals, and children who had finished early chores slipped into the lanes with the restless energy of those who still believed a day might become play if no adult caught them first. Jesus worked steadily. He brought Joseph the plane, gathered cuttings, held the far end of a board, and listened when Joseph explained how a weakened piece could sometimes be made useful again if joined properly and not forced beyond its strength. He listened with the whole of Himself, though part of His attention remained turned toward the house with the leaning wall.
Eliab appeared just before the sun climbed high enough to warm the stones. He came carrying a basket of wool scraps and torn garments, the load pressed against his chest. His hair was uncombed, and the strap of one sandal had been tied with a strip of cloth. He moved quickly, as if speed could keep him from being stopped. Two other boys, Natan and Joah, trailed behind him with the cruel curiosity of children old enough to know where to wound and young enough to pretend it was nothing.
“Careful,” Natan called. “If you drop those, your mother will have to sew the dirt back together too.”
Joah laughed. “Maybe Eliab can mend his sandal with his father’s old belt. Oh, I forgot. He sold it.”
Eliab’s face hardened, but he did not turn. His hands tightened around the basket until his knuckles whitened. Jesus set down the small wedge of wood He had been smoothing. Joseph had heard, and his jaw set, but he did not move yet. A rebuke from a grown man might silence the boys for a morning and make Eliab pay for it later in whispers. Jesus stepped from the shade of the work area and walked into the lane.
Natan saw Him and shifted his weight. He was older than Jesus by a year and enjoyed the advantage when it was easy. “We were only speaking.”
Jesus looked at him without anger. “Were you speaking to help him carry the basket?”
Natan’s mouth opened, then closed. Joah kicked at a stone.
Jesus went to Eliab and placed His hands beneath one side of the basket. “I can carry it with you.”
Eliab flinched at the offer more than he had flinched at the insult. “I do not need help.”
“I did not say you were weak.”
“I said I do not need help.” Eliab pulled the basket closer, nearly losing hold of it. A torn sleeve fell from the top and landed in the dust.
Jesus bent, picked it up, shook it clean, and laid it back without making the moment larger than Eliab could bear. “Then I will walk beside you.”
That seemed almost worse to Eliab, because help could be refused but presence had nowhere to be sent. He started forward again. Jesus walked at his side, not touching the basket now. Natan and Joah followed for a few steps but lost interest when no anger came to feed them. Joseph returned to the plow beam, though his eyes lingered. Mary watched from the doorway with the look of a mother who understood both boys more than either would have wanted.
The lane narrowed past the well, where several women stood speaking in low voices. As Eliab approached, their conversation changed shape. No one said anything unkind. That was part of the heaviness. Their pity came wrapped in lowered tones and softened faces, and Eliab felt every bit of it like dust clinging to sweat. Mara, his mother, was known to be proud in the way the poor become proud when they are tired of being measured by what is missing. Since her husband’s death, she had accepted grain once from an older cousin and had returned twice its worth in mending. After that, she had found ways to appear grateful without ever appearing in need.
Eliab walked faster. Jesus kept pace.
“You should go back,” Eliab muttered.
“I will, after you reach your house.”
“People will think I asked you.”
“No one has to know what they do not need to know.”
Eliab glanced at Him then, suspicious of gentleness that did not demand recognition. “Why do you care?”
Jesus looked ahead to the leaning wall. “Because you are carrying more than cloth.”
The words struck the place Eliab had sealed shut. His face changed for an instant, not into openness but into fear, as if Jesus had put His hand on a hidden latch. “Do not say things like that.”
“I will not say more now.”
They reached the courtyard. The gate hung unevenly, and the clay jar near the entrance had a crack that had been sealed with pitch. From inside came a cough, then the scrape of a stool. Mara appeared in the doorway with a needle tucked into the cloth at her shoulder and dark circles beneath her eyes. She looked first at Eliab, then at Jesus, and something like embarrassment crossed her face.
“Jesus,” she said, gathering herself quickly. “Peace to you.”
“Peace to your house,” He answered.
Eliab set the basket down too hard. “He followed me. I told him not to.”
Mara’s eyes moved over her son, reading more than his words. “Then thank him, even if you did not ask.”
“I do not need every person in Nazareth thinking we cannot carry our own basket.”
The courtyard grew still. Mara’s face tightened, not with anger first, but with weariness exposed too suddenly. “Go inside and wash your hands.”
“I have work.”
“You have a mouth that is running ahead of wisdom. Go inside.”
Eliab’s shoulders lifted as if he might argue, but he looked at Jesus and seemed ashamed of being witnessed. He snatched the basket again and pushed past his mother into the house.
Mara closed her eyes briefly. “Forgive him. He is not himself.”
Jesus did not look away from the doorway where Eliab had vanished. “He is afraid he is all that is left.”
Mara’s hand went to the doorframe. The words did not offend her. They tired her because they were true. “He heard men talking after the burial. They said a widow’s house is a sinking roof unless a son learns quickly. They did not know he was behind the wall.”
Jesus turned back to her. “Does he think he must become his father?”
“He thinks if he does not, we will lose everything.” Mara tried to smile and could not make it stay. “He was gentle before. He used to sing nonsense to the goats and make his little sister laugh until she spilled water. Now if she laughs too loudly, he tells her to save her strength. He counts the grain. He watches my hands. He wakes when I cough. Sometimes I find him sitting by the tools as if staring at them long enough will teach him how to be a man.”
“Where is his sister?”
“With my sister today. I had too much work to keep her from pulling the thread.”
Inside the house, something wooden struck the floor. Mara winced but did not turn. Pride fought concern on her face and lost. “I should go in.”
Jesus stepped back. “I will tell my mother you may need oil for the lamp.”
Mara’s eyes sharpened. “I did not ask for oil.”
“No,” Jesus said gently. “You stayed awake without it.”
For a moment, Mara looked as if she might refuse the kindness before it had even been offered. Then her shoulders lowered, just a little. “Tell your mother nothing that will make the women speak.”
“I will tell her only what love needs to know.”
Mara’s mouth trembled. She pressed her lips together and nodded once, then went inside.
Jesus returned through the lane slowly. The village had become bright now, full of sound and sun, but the morning’s prayer had not left Him. He passed the well where the women still talked. One of them, an older woman named Tirzah, touched His shoulder lightly.
“You were at Mara’s house?”
“Yes.”
“She will not accept help.”
Jesus looked up at her. “Then perhaps help should arrive without shaming her.”
Tirzah sighed. “That is more difficult.”
“Yes,” Jesus said.
The woman studied Him, then gave a small, almost puzzled smile. “You speak like your mother when she is quiet and like Joseph when he has decided not to be hurried.”
Jesus received that without pride and continued home.
By noon, the heat pressed down on the roofs, and work slowed. Joseph set aside the plow beam and shared bread with Jesus in the shade. Mary had sent a small bowl of olives and a piece of goat cheese, and they ate simply. Jesus asked whether there was extra oil in the house. Joseph looked toward Him with the attention he gave to wood before deciding where to cut.
“For Mara?”
Jesus nodded.
Joseph broke his bread in two and gave Jesus the larger piece without comment. “There is some. Not much.”
“Enough for tonight?”
“Enough for tonight.”
Jesus looked at the bread in His hand. “She will not want to receive it.”
“No,” Joseph said. “Sometimes people who have been wounded by loss feel wounded again by kindness. It tells them the loss is visible.”
Jesus sat with that. Across the lane, a little girl ran after a chicken and laughed. The sound floated briefly and then disappeared behind a wall. Jesus thought of Eliab telling laughter to save its strength.
“Can a boy become hard because he is trying to be faithful?” Jesus asked.
Joseph wiped his hands and leaned back against the wall. “Yes. A man can too.”
“Then someone must show him that faithfulness is not the same as fear.”
Joseph’s eyes rested on Jesus for a long while. “And how will you show him?”
Jesus looked toward Eliab’s house. “By staying near enough for him to become angry at mercy.”
Joseph did not smile, though tenderness moved across his face. “That may be costly.”
Jesus lowered His eyes. “Mercy often is.”
The afternoon brought the first consequence. Eliab came running to Joseph’s work area with his face pale and his breathing broken. Sweat darkened his tunic at the neck. He stopped at the edge of the shade as if the threshold itself accused him.
“The shelf,” he said.
Joseph rose at once. “What shelf?”
“My father’s shelf. In the house. It came loose. The jars fell.” His voice tightened. “One broke. The oil.”
Jesus stood too, already understanding more than the words carried. “Was anyone hurt?”
“No.” Eliab swallowed. “My mother tried to catch it, but it struck her wrist. She says it is nothing. It is not nothing.”
Joseph reached for his tool bundle. “I will come.”
Eliab’s eyes filled with panic. “We cannot pay.”
“I did not ask.”
“I can work. I can sweep. I can carry wood. I can—”
“Eliab,” Joseph said, firm but not harsh, “a loose shelf does not wait until a house can afford it.”
The boy looked cornered by mercy again. His gaze shifted to Jesus, and something wounded in him turned sharp. “You told them.”
Jesus met his anger quietly. “I told no one about the shelf.”
“You told them we needed oil.”
“I asked because your lamp had burned late.”
“You saw too much.”
Jesus did not deny it. “I saw a light in a tired house.”
Eliab’s eyes flashed. “You think that makes you good?”
Joseph paused, tool bundle in hand. The lane seemed to quiet around them. Jesus stood very still, not offended, not retreating. “No.”
The answer was so simple that Eliab seemed not to know where to put his anger. His mouth twisted, and for a moment he looked younger than twelve, younger than grief had allowed him to be. Then he turned and hurried back toward his house, leaving Joseph and Jesus to follow.
Inside Mara’s home, the shelf had pulled from the wall where old clay had crumbled around the wooden peg. Two jars lay cracked on the floor, and a dark stain of oil had spread into the dust. Mara sat near the hearth with her wrist held against her chest, refusing to weep from pain or humiliation. The room smelled of spilled oil, broken clay, and the faint sourness of fear. Eliab stood in the corner, rigid, watching Joseph examine the wall. He looked as if every crack in the house were a charge against him.
Joseph worked without ceremony. He did not speak of payment. He did not make pity visible. He asked Jesus for the smaller peg, then the mallet, then a strip of leather to brace the weakened place. Jesus moved quietly, each action careful, while Mara’s eyes followed Him. Eliab did not help at first. He hovered, tense with the uselessness he hated.
At last Joseph said, “Eliab, hold this steady.”
The boy stepped forward too quickly, eager for a task that sounded like proof. He gripped the shelf while Joseph reset the support. Jesus stood on the other side, holding the brace. Their hands came close but did not touch. Eliab stared at the wood.
“My father made this,” he said, almost too low to hear.
Joseph did not stop working. “Then we will honor his work by strengthening it.”
“It failed.”
“It carried weight for many years.”
“It failed when we needed it.”
Joseph’s hands slowed. Jesus looked at Eliab, but the boy kept his eyes on the shelf. The words were not about wood. Everyone in the room knew it, and because they knew it, no one rushed to answer.
Mara made a small sound. “Eliab.”
He shook his head. His grip tightened. “It failed.”
Jesus spoke softly. “Your father did not fail because he died.”
Eliab’s face went white. “Do not speak of him.”
Jesus did not move closer. “You are trying to hold up what only God can hold.”
“Be quiet.”
Joseph’s eyes flicked toward Jesus, not warning Him away, but weighing the moment. Mara covered her mouth. The repaired shelf creaked as Eliab’s hands trembled against it.
Jesus continued, His voice still gentle. “You loved him. You miss him. You are angry that he is gone. And you are afraid that if you stop being strong, your house will fall too.”
Eliab released the shelf as if burned. The wood shifted, and Joseph caught it with one hand. “I said be quiet!”
The shout filled the little room. Outside, a goat bleated, absurdly ordinary. Mara began to stand, but pain pulled her back. Eliab looked at his mother, then at Joseph, then at Jesus, and shame rushed in after anger. He backed toward the doorway.
“I will get more clay,” he muttered.
Joseph said his name, but Eliab was already gone.
For a few breaths, no one spoke. Jesus looked toward the open door, where sunlight lay across the threshold. He had not resolved the wound. He had opened it. That was different, and it hurt more.
Mara’s eyes shone with tears she would not let fall. “He has not said he misses him. Not once.”
Jesus bent and picked up a broken piece of the oil jar. He held it carefully so the sharp edge would not cut Him. “He thinks missing him will make him less able to protect you.”
Mara looked at her wrapped wrist. “And I have let him think it, because I was afraid if he became a child again, I would have no one standing beside me.”
Joseph lowered the shelf into place and set the brace. His voice was quiet. “A child should not have to become a husband to his mother.”
Mara’s face broke then, not loudly, but in a way that seemed to take strength from her whole body. She turned aside, pressing her injured wrist against her chest, and wept without covering it quickly enough. Jesus did not stare at her tears. He set the broken clay aside and waited as if sorrow were not something shameful that needed to be hidden before God could enter the room.
When the shelf was secure, Joseph gathered the pieces of broken jar and carried them out. Jesus remained long enough to sweep the spilled dust and oil into a small dark mound near the doorway. Mara watched Him, breathing unevenly.
“Will he hate You for saying it?” she asked.
Jesus looked toward the lane where Eliab had disappeared. “He may hate being seen before he is ready to be healed.”
“And what do we do with that?”
Jesus lifted the broom and rested it against the wall. “We do not stop loving him when he makes love difficult.”
Mara closed her eyes. The words landed in the room with a weight that did not crush. They simply stayed.
When Jesus stepped back into the sunlight, Eliab was nowhere near the clay pit or the lane. Jesus looked toward the lower terraces where boys sometimes went when they did not want to be found. Joseph came beside Him, carrying the tool bundle.
“Will you go after him?” Joseph asked.
Jesus watched the heat tremble above the stones. “Not yet.”
Joseph nodded. “Why?”
“Because he ran from truth, not from danger. If I follow too soon, he will only run farther.”
They walked home together. The village carried on around them. Someone bargained over figs. A woman scolded a child for splashing at the well. A donkey refused to move until its owner gave up shouting and pulled with both hands. Life did not pause because one boy had been exposed in his grief. That was part of the sorrow of the world. People could break inside while the market still opened, the bread still baked, and neighbors still asked ordinary questions.
Jesus returned to Joseph’s work area, but the day had changed. The repaired plow beam waited, yet His thoughts stayed with Eliab. He could still see the boy’s hands trembling against the shelf, still hear the anger that had risen because sadness had no other door. Mary brought water in the late afternoon, and Jesus drank. She touched His hair lightly, smoothing back dust.
“You spoke truth today,” she said.
Jesus looked up at her. “It hurt him.”
“Yes.”
“He was already hurting.”
“Yes.”
Jesus held the cup with both hands. “Truth can feel like another wound when someone has been hiding the first one.”
Mary sat beside Him in the shade. “And yet hidden wounds do not become clean by staying hidden.”
He looked toward the hills. The sun had begun its slow descent, softening the village edges. Somewhere below, Eliab was alone with the thing he had been trying not to know. Jesus knew He would see him again before night. He also knew the next meeting would not be easier.
As evening approached, Joseph sent Jesus to return a borrowed awl to a man whose courtyard looked over the lower path. Jesus took the tool and went alone, not because He needed to pass near the terraces, but because obedience often moved through ordinary errands. He returned the awl, accepted the man’s blessing, and began the walk back as shadows gathered. Near the low stone wall beyond the last houses, He heard the sound of someone striking rock with a stick.
Eliab stood among the scrub and stones, hitting the ground again and again until the stick splintered. His face was wet, though whether from sweat or tears was hard to tell in the fading light. He saw Jesus and froze.
“Go away,” he said.
Jesus stopped several paces off. “I am on the path home.”
“Then keep walking.”
Jesus looked at the broken stick in Eliab’s hand. “Does the ground answer when you strike it?”
Eliab’s jaw clenched. “You think everything you say means something.”
“No.”
“You said I was afraid.”
“You are.”
Eliab lifted the stick as if he might throw it, then lowered it. “My father said he would teach me how to fit a door before winter. He said I was old enough to learn properly. Then he became hot with fever, and men carried him out, and everyone kept saying God is merciful.” His voice cracked on the last word. “What does that mean when the door still does not fit and my mother sits awake because there is not enough oil?”
Jesus listened. The wind moved lightly through the dry grass. From the village, faint voices carried upward, blurred by distance.
Eliab wiped his face angrily. “If I miss him, I cannot work. If I cry, my mother will cry. If I am a child, we will starve. So tell me, Jesus. What am I supposed to do with all that?”
Jesus did not answer quickly. He stepped closer, only one pace. “Bring it to God without pretending it is smaller.”
Eliab gave a bitter laugh. “That is what people say when they have bread.”
Jesus received the accusation without defense. “Then say that to Him too.”
The boy stared at Him.
Jesus’s voice remained quiet. “If you think God has been hard with you, do not speak to Him as if you think He has been gentle. If you are angry, do not dress anger like obedience. If you are afraid, do not call fear responsibility. He already knows what is true. Prayer is not where you hide from Him. It is where you stop hiding.”
Eliab’s breathing changed. The stick slipped from his hand. “I do not know how.”
Jesus looked toward the village, where lamps were beginning to appear one by one. “Then begin with what you just said.”
“I cannot.”
“Not yet,” Jesus said. “But you will have to choose. You can keep trying to become your father, or you can let God be Father to you in the place where yours is gone.”
Eliab turned away, but not before Jesus saw the tears come fully. The boy covered his face with both hands and bent forward under the force of what he had held back for months. Jesus did not touch him. Not yet. He stood near in the falling light while Eliab wept like someone who had finally stopped guarding a door that had already been broken.
The village lamps brightened. Somewhere in Nazareth, Mara waited with an injured wrist and a repaired shelf. Joseph’s work lay unfinished for morning. Mary tended the hearth. The day that began in prayer had led to a boy standing among stones with grief uncovered, and still nothing was fixed completely. That was how mercy often began. Not with everything healed, but with the first honest sound after a long silence.
Chapter Two
Eliab did not go home quickly after the tears stopped. He stood with his back to Jesus and wiped his face on his sleeve until the cloth was damp and streaked with dust. The sky had deepened into evening, and the first coolness came down from the hills, touching the stones that had spent the day holding heat. He looked embarrassed by the silence more than by the weeping itself, as if silence gave memory too much room to speak.
Jesus waited on the path, close enough to remain with him and far enough not to trap him. The village below them had begun to gather into night. Lamps burned behind small openings. Smoke rose from roofs. Voices softened as families came inside. Nazareth looked peaceful from where they stood, but Eliab knew what waited beneath that peace. His mother would ask where he had gone. His sister would ask why his eyes were red. The shelf would be repaired, but the oil was gone. The house would still be the house where his father did not sit.
“You should not tell anyone,” Eliab said at last.
“I will not tell what is yours to speak.”
Eliab turned enough to look at Him. “People already talk.”
“Yes.”
“They say things even when they pretend not to.”
“Yes.”
“They look at my mother as if she is a cracked jar.”
Jesus looked toward the village. “Some people do not know how to see pain without making the person feel smaller.”
Eliab pressed his lips together, because that was exactly what he hated and could not have said so clearly. “I hate it when they bring bread.”
“Because you need it?”
“Because they know we need it.”
Jesus nodded. “That can feel heavy.”
“It is heavy.” Eliab kicked a loose stone, sending it down the slope until it struck the wall below. “If my father were here, no one would bring bread.”
Jesus did not argue, though both of them knew there were houses with fathers where hunger still entered. This was not the moment to correct every thought. Some words were not meant to be measured first. They were meant to be brought out of the dark where they had grown too large.
After a while, Eliab said, “I do not want my mother to see me like this.”
“She may need to.”
“No.” The answer came quickly, with fear under it. “She has enough.”
Jesus turned toward him. “Does she have you?”
Eliab frowned. “What does that mean?”
“Does she have her son, or does she only have the guard you have placed at the door?”
The boy looked away. His face tightened again, not with anger this time, but with the strain of understanding something before he was ready to accept it. “If I stop, everything falls.”
“You are not holding everything.”
“You do not know that.”
Jesus’s eyes were steady. “I know you are tired.”
Eliab swallowed hard. The truth had become less like a blade and more like a hand resting on his shoulder, which made it harder to fight. He bent, picked up the broken stick, and turned it over in his hands. “I should go.”
“I will walk behind you.”
“Why behind?”
“So you do not have to feel watched.”
Eliab gave Him a suspicious glance, but he did not refuse. They descended toward the village with several paces between them. Jesus moved quietly. Eliab walked faster when they passed houses where voices could be heard. At his own courtyard, he stopped so suddenly that Jesus stopped too. The doorway glowed with low lamplight. Mara’s shadow moved across the wall inside. A smaller shadow moved after hers, quick and uneven, and Jesus knew Eliab’s little sister had returned.
Eliab did not enter.
From inside, the girl’s voice rose. “Mother, will Eliab come back before the bread is gone?”
Mara answered with forced calm. “He will come.”
“He is always angry.”
“He is not always angry.”
“He told me not to sing.”
Mara’s answer came late. “Then sing quietly tonight.”
Eliab’s face changed as if the words had struck him harder than Natan’s mockery. He had not known his anger had entered his sister’s little joys and told them where to sit. He stared at the doorway with shame gathering under his eyes.
Jesus did not speak. He simply stood behind him on the path.
Eliab stepped inside. Jesus remained outside the courtyard wall, unseen by Mara at first. He heard the small shift in the room when Eliab entered, the way silence can announce a person more loudly than a greeting.
“Where were you?” Mara asked.
Eliab’s voice was low. “By the lower stones.”
“You frightened me.”
“I know.”
His sister, Dalia, spoke with the bluntness of six years. “Your face is dirty.”
Eliab did not snap at her. “I know.”
Mara must have seen more then, because her voice softened. “Come here.”
“I am fine.”
“No,” she said, and there was a tremble in the word that did not weaken it. “Come here as my son, not as the man of the house.”
Eliab did not move. Jesus could not see him, but He could feel the resistance in the pause. The boy’s whole false life stood at that threshold. To cross it would mean letting his mother see the child grief had buried alive. To refuse would mean keeping the house in its cold order, where no one sang loudly and no one cried safely.
“I do not know how,” Eliab said.
Mara wept then, not much, but enough that Dalia became quiet. “Neither do I.”
That honesty entered the house like fresh air through a room closed too long. Eliab made a sound that was almost a breath and almost a sob. Jesus heard the scrape of a stool, then the soft collapse of someone kneeling. Mara whispered her son’s name. Dalia asked if she should bring water, and for the first time in many months, Eliab laughed through tears. It was brief and broken and full of pain, but it was laughter.
Jesus turned to go. He did not need to be seen in that moment. Mercy had reached the door, and the door had opened from the inside.
When He returned home, Mary was waiting with a bowl covered by cloth. She did not ask many questions. She looked at His face and understood enough. Joseph sat near the doorway repairing a strap by lamplight. He glanced up, then toward the bowl.
“Your mother kept food warm.”
Jesus washed His hands and sat with them. The house smelled of lentils and bread, and the quiet there was different from the quiet in Mara’s house. It held trust. Jesus ate slowly. Mary watched Him in the way mothers watch children who carry more than the day should have given them.
“Did he go home?” she asked.
“Yes.”
“Did he speak?”
“Yes.”
Joseph tied off the strap and set it aside. “Then the first gate has opened.”
Jesus looked at the small flame between them. “The gate is open, but the road is still hard.”
Joseph nodded. “A boy can tell the truth in the evening and still be afraid by morning.”
That proved true before the sun had risen fully the next day. Eliab came to Joseph’s work area carrying two of his father’s tools wrapped in cloth. His eyes were swollen, but his jaw had returned to its stubborn line. He waited until Joseph looked up, then laid the bundle down as if he were placing an offering on an altar.
“I want you to teach me to use these,” he said.
Joseph wiped sawdust from his hands. “Good tools.”
“They were my father’s.”
“I know.”
“I need work.”
Joseph did not touch the bundle yet. “You need to learn.”
“I can learn while working.”
“You can learn by watching first.”
Eliab’s mouth tightened. “Watching does not buy oil.”
Jesus, who had been smoothing a small peg, looked up. The words were honest, but fear had dressed itself in responsibility again. It had only changed garments overnight.
Joseph unfolded the cloth. Inside lay a chisel with a worn handle and a small adze, both cared for but unused since Eliab’s father died. Joseph lifted the chisel and tested its edge. “This needs sharpening.”
“I can sharpen it.”
“Have you sharpened one before?”
“I have seen him do it.”
Joseph set the chisel down carefully. “Seeing is not the same as knowing.”
Eliab’s face burned. “Then teach me quickly.”
“There are things that cannot be taught quickly without harming the learner or the work.”
“I do not have time to be a child.” The words came out louder than he intended. A passerby looked over, and Eliab’s shoulders stiffened.
Jesus rose and came near, but He did not enter the conversation too quickly. Joseph folded the cloth back over the tools, not dismissing them, simply covering them from the dust.
“Eliab,” Joseph said, “I can teach you. I will not make you into your father by sundown. I will not pretend you can carry a man’s trade before your hands are ready. That would not honor him.”
“My mother needs coin.”
“Your mother needs a son who does not cut his hand open trying to prove he is a man.”
Eliab looked away.
Joseph’s voice softened. “Come three mornings each week after your first chores. Sweep, carry, watch, ask. When your hands are ready, you will shape small pieces. When those are true, you will shape larger ones. If work comes that can be paid fairly to a learner, I will tell you. But I will not put fear in charge of the tools.”
The offer was kind, measured, and humiliating to the part of Eliab that wanted urgency to become adulthood. He looked at Jesus as if expecting Him to add something. Jesus only said, “A tool obeys the hand that has learned patience.”
Eliab almost smiled despite himself, but pride caught it. “Everything with You becomes patience.”
“Not everything,” Jesus said. “Some things become surrender.”
The word unsettled him more than he wanted to show. He snatched up the covered tools. “I will come tomorrow.”
Joseph nodded. “Come before the heat.”
Eliab left, and for a little while hope seemed possible. But rising truth often awakens the very fear it threatens, and by midmorning Eliab’s fear had found another road. Mara sent him to the well with a jar that had survived the broken shelf. Dalia followed, singing under her breath because the night before had given her permission again. Eliab let her sing until they neared the well and saw Natan and Joah sitting on the low stones with two other boys. Then he turned sharply.
“Stop.”
Dalia’s song died. “Why?”
“Just stop.”
She hugged the small cup she carried. “Mother said I could sing.”
“Not here.”
The boys noticed them. Natan leaned back, grinning. “Eliab, did you cry so loudly last night that the dogs hid?”
Joah laughed. “Maybe Jesus taught him to weep properly.”
Eliab’s hand tightened on the jar rope. Dalia looked from the boys to her brother, frightened by the change in him. At the edge of the well path, Jesus had come with Mary to draw water, though He remained a little behind her with another jar. He saw the moment take shape before anyone else did. Eliab had been seen in weakness, and now shame demanded payment from someone smaller.
Natan hopped down from the stone. “Careful with that jar. If you break another one, your mother will have to borrow from every house in Nazareth.”
Eliab stepped forward. “Say her name again.”
Natan’s grin faltered, then returned because the other boys were watching. “Mara, Mara, Mara.”
Eliab swung the jar. He did not mean to strike Natan’s head, but anger rarely asks where it will land once it is allowed to lead. The jar clipped Natan’s shoulder and flew from Eliab’s hand, breaking against the stones near the well. Water spread across the dust. Dalia screamed. Natan stumbled back, more shocked than injured, and Joah shouted for his mother. The women at the well turned all at once. Mary moved quickly to Dalia and drew her aside. Jesus stepped between Eliab and the boys before another blow could come.
The scene hardened around Eliab. Every face looked at him. Every whisper he hated had become possible now. Natan rubbed his shoulder, red-eyed with embarrassment. “He hit me.”
“You mocked his mother,” one woman said, but her correction came too late to undo the broken jar.
Eliab stared at the shards as if he had awakened and found his own hands guilty. The jar had been one of the last good ones. He looked at Dalia, whose small mouth trembled. He looked at Jesus and saw no accusation there, which somehow made it worse.
“I did not mean to break it,” he said.
Natan, recovering his pride, spat toward the ground. “Widow’s son cannot even carry water.”
Eliab lunged again, but Jesus caught his wrist. He did not grip hard, yet Eliab could not pull free. The strength in that small hand startled him. Jesus looked into his face with a sadness that held him more firmly than fingers.
“If fear leads you,” Jesus said, “it will make you harm the people you are trying to protect.”
Eliab’s breath shook. “Let me go.”
“I will. But not into more sin.”
The word pierced him. Sin was not a word adults used for grief, and Eliab wanted grief to excuse everything that followed it. He pulled back, and Jesus released him. The boy stood surrounded by water, shards, staring villagers, and the crying sister he had silenced once again.
Mary knelt and began gathering the larger pieces so no child would cut a foot. Dalia clung to her. Natan’s mother arrived in a rush, full of anger and worry. She examined her son’s shoulder, then rounded on Eliab.
“Has your house lost all discipline?”
Mara arrived moments later, drawn by the shouting. Her injured wrist was wrapped, and her face showed that she had come too fast. She saw the broken jar, Dalia crying against Mary, Natan’s mother furious, and Eliab standing in the middle of it all with shame closing around him.
“What happened?” Mara asked.
No one answered gently. Several spoke at once. The story became tangled with accusation, defense, pity, and judgment. Mara’s face went pale. Eliab stared at the ground and did not defend himself. That silence, which once had looked like strength to him, now looked like cowardice.
Jesus stepped beside him. “Natan mocked Mara. Eliab struck with the jar and broke it. Natan was not badly hurt, but Eliab did wrong.”
The clear truth quieted the crowd because it belonged to no side. Natan’s mother drew herself up, still angry but robbed of exaggeration. Mara closed her eyes. Eliab looked at Jesus with betrayal in his face.
“You told against me.”
Jesus looked at him steadily. “I told the truth for you before shame could make it crooked.”
Eliab’s lips parted, but no words came.
Mara turned to Natan’s mother. “I am sorry for my son’s hand against yours. We will make right what we can.”
Natan’s mother looked toward the broken jar and then back at Mara’s wrapped wrist. Her anger shifted uneasily under the eyes of the women. “See that he keeps away from my boy.”
Mara nodded. Then she turned to Eliab. “Pick up what broke.”
The command was simple, and he obeyed because there was nothing else left. He knelt among the shards, careful now, slow now, feeling each piece of clay as evidence. Dalia watched him from Mary’s side. When he reached for one sharp fragment, Jesus bent and moved his hand away.
“That one will cut you.”
Eliab whispered, “Good.”
Jesus’s face changed, not with shock, but with deeper grief. “No.”
The single word was quiet enough that no one else seemed to hear it. Eliab did. It entered the place where punishment had started to look like relief.
Jesus picked up the sharp piece Himself and placed it with the others. “You cannot pay for wrong by wounding what God made.”
Eliab’s eyes filled again, but this time he fought the tears because the village was watching. “Then what do I do?”
Jesus looked at Dalia, then at Mara, then at Natan standing behind his mother. “You begin by saying the truth without hiding behind what was done to you.”
Eliab’s throat worked. He looked at Natan, and anger still moved there. He looked at his mother and saw exhaustion. He looked at his sister and saw fear of him, which hurt most of all.
“I struck him,” Eliab said, barely audible.
Mara’s voice came softly. “Louder, son.”
He swallowed. “I struck him. I broke the jar. I frightened Dalia.” He looked at Natan’s mother, though the words seemed to cost him more than lifting any load. “I was wrong.”
No one applauded. Real repentance did not need a crowd to reward it. Natan looked uncomfortable. His mother held his shoulder a little less tightly. The women at the well shifted, some ashamed of their interest now that the spectacle had become holy in a way they had not expected.
Jesus stood beside Eliab as he gathered the last pieces. The water had already sunk into the dust. Nothing about the moment restored the jar, the oil, the father, or the months of fear. But something true had happened in public, and truth in public has a different cost than truth in the dark. Eliab had not been rescued from consequence. He had been kept from lying to survive it.
When the shards were gathered, Mara took the cloth bundle from him. “Come home.”
Eliab nodded, but before he followed, he turned toward Jesus. His face was full of hurt, anger, gratitude, and confusion all at once. “I thought You were helping me.”
Jesus looked at the broken pieces in Mara’s hands. “I am.”
Eliab wanted to reject the answer. He wanted help to mean protection from embarrassment, rescue from cost, silence before accusation, bread without being seen, strength without surrender. Instead, Jesus had stood with him and told the truth. The boy did not yet know how mercy could feel so much like being uncovered.
He followed his mother away from the well, Dalia walking close to Mary until Mara reached back with her good hand. Dalia hesitated, then took it. Eliab saw that hesitation and lowered his head.
Jesus remained by the well after they left. Mary came beside Him, still holding a few fragments she had gathered. The women resumed their drawing of water, quieter now. Natan and Joah slipped away, their laughter gone for the moment.
Mary looked at Jesus. “That was a hard mercy.”
Jesus watched Eliab’s family disappear behind the turn in the lane. “He asked what to do.”
“And now?”
“Now he must learn that repentance is not the end of love. It is the place where love can finally begin to rebuild what fear has broken.”
Mary placed the fragments into the cloth with the others. “Will he let it?”
Jesus looked toward Mara’s house, where the repaired shelf waited and the broken jar would soon be set down beside it. “He will be tempted not to. Shame will tell him to become hard again.”
The wind lifted dust along the path, then settled. Jesus turned back toward the well, where the rope creaked under another full jar.
“So we will stay near.”
Chapter Three
Mara did not speak until they were inside the courtyard. She set the broken jar pieces on the ground near the doorway and stood over them as if she could still command them back into their old shape by looking long enough. Dalia slipped behind her skirt, quiet now, one hand twisted into the fabric. Eliab carried nothing. That made his hands feel worse than full. They hung at his sides, useless and guilty, while the house waited around him with its repaired shelf, its dim corner where his father’s tools used to rest, and the thin smell of yesterday’s spilled oil still caught in the dust.
Mara turned slowly. Her face held anger, but beneath it was something that frightened him more. She looked hurt by him. Not by the village, not by hunger, not by death, but by her own son. Eliab had been prepared for scolding. He had been prepared for silence. He had not been prepared for the way his mother looked smaller because of something he had done.
“Did he strike you first?” she asked.
“No.”
“Did he threaten Dalia?”
“No.”
“Did he mock this house?”
Eliab lifted his eyes. “Yes.”
Mara breathed in through her nose, steadying herself. “And you thought breaking one of our jars would defend it?”
“I did not think.”
“That is true.” Her voice did not rise, and somehow that made it worse. “You did not think of your sister standing beside you. You did not think of my wrist. You did not think of the water we needed. You did not think of the shame that would come when everyone saw our house in another broken thing.”
Eliab flinched. “I said I was wrong.”
“You said it at the well because Jesus told you to say it. I am asking whether you know it here.”
Dalia pressed closer to Mara. Eliab saw the movement and felt something tear quietly inside him. The day before, his sister had laughed through his tears. This morning, she had hidden from his anger. He wanted to tell her not to be afraid of him, but wanting her not to be afraid was not the same as being safe.
Mara knelt with difficulty and began sorting the pieces of jar, placing larger fragments in one pile and smaller ones in another. Her injured wrist made the work awkward. Eliab stepped forward to help, but she shook her head.
“Not yet.”
The refusal hurt more than if she had shouted. He stood there while his mother gathered what he had broken. Dalia watched the door, as if hoping someone would come and change the room. No one came. The house had to sit with the truth.
At last Mara said, “Go to the back wall. Bring the small basket.”
Eliab obeyed at once. The basket was old and bent, used for scraps that might still serve some purpose. When he returned, Mara placed the broken pieces inside. Every small clink sounded to him like a word.
“We will keep them,” she said.
“Why?”
“Because I cannot afford to forget what anger costs.”
The words were not cruel. That was why they stayed. Eliab stared at the basket. He wanted punishment that would be over quickly. A strike. A command. A day without bread. Something simple enough that he could pay it and step out from under the weight. Instead, his mother had made the broken jar into a witness.
“What do you want me to do?” he asked.
Mara looked toward Dalia, then back at him. “First, you will speak to your sister.”
Dalia’s eyes widened. “I do not need him to.”
“Yes,” Mara said gently, “you do.”
Eliab crouched because Dalia was small and because standing over her suddenly felt wrong. She looked at him from behind their mother’s side, her lower lip caught between her teeth.
“I frightened you,” he said.
She nodded.
“I told you not to sing.”
She nodded again.
“I should not have done that.”
Dalia looked at the floor. “You said singing wastes breath.”
Eliab closed his eyes. He remembered saying it. He had been counting grain, and she had been making up a song about a goat with a crooked horn. Her happiness had filled the room while he was afraid of the empty jar, and he had struck at the happiness because he could not strike at the fear. “I was wrong.”
“Can I sing now?” she asked.
The question should have been easy. It was not. Something in him still tensed at joy, as if joy were careless in a house that could not afford oil. He looked at his mother, then at the floor, then back at his sister. “Yes.”
Dalia studied him with the grave suspicion of a child who wants to believe good news but remembers disappointment. “Loud?”
His throat tightened. “Not while Mother’s head hurts.”
Mara’s mouth softened for the first time that day. Dalia considered the compromise and accepted it. She hummed, barely at first, then a little stronger. The small sound moved through the room like a candle being protected by two hands. Eliab sat back on his heels and felt both relief and grief. He had not known how much quiet he had forced upon them.
A shadow fell across the doorway. Jesus stood outside the threshold with a small clay lamp in His hands. He did not step in until Mara saw Him.
“My mother sent this,” He said. “It is not new, but it will hold oil.”
Mara looked at the lamp and then at Eliab. Pride rose in her face by habit, ready to guard the door. But she had wept the night before, and some defenses, once opened, do not close as tightly. “Your mother has already given too much kindness.”
Jesus held the lamp with both hands. “Then let this be kindness that teaches us how to receive.”
Mara’s eyes lowered. “Come in.”
Jesus entered and set the lamp near the repaired shelf. Dalia’s humming stopped when He came close, then began again, softer, because His presence did not shame it. Eliab watched Him place the lamp exactly where the broken jar had fallen, and he felt exposed all over again.
“You saw everything,” Eliab said.
Jesus turned toward him. “At the well?”
“And here. Somehow You see here too.”
Jesus looked around the small room, not with curiosity but with reverence, as if poverty did not make a house less worthy of gentleness. “Your house has been speaking loudly for a long time.”
Eliab almost answered sharply, but the basket of broken clay sat beside him. He had no strength for pretending. “What is it saying?”
“That everyone inside is trying not to be the one who falls apart.”
Mara looked away. Dalia stopped humming. Eliab felt the truth move from person to person like light touching hidden things. He wanted to reject it and could not.
Jesus came nearer and sat on the floor, not on the stool, not above them. The lamp stood between Him and the broken pieces. “When your father died, sorrow entered this house. That was heavy enough. But fear came after it and told each of you to stand alone. It told your mother she must never receive too much. It told Dalia her songs were dangerous. It told you that love meant becoming hard before anyone could see you were afraid.”
Eliab’s eyes burned. “If I had been older, I could have helped him.”
Mara made a sound. “No, son.”
“If I had known what to do, if I had fetched someone sooner, if I had kept him cooler—”
“You were a child,” Mara said, and this time the words broke open with months of pain. “You were my child. You brought water. You sat by him. You held his hand when he asked. You did not fail him.”
Eliab shook his head hard. “He looked at me like he needed something.”
“He looked at you because he loved you.”
The room seemed to tilt. Eliab had carried that look as a command. In fever and weakness, his father’s eyes had searched for him, and Eliab had decided they were asking him to take his place. Now his mother was saying they had been giving love, not assigning a burden. It was too much to receive all at once.
Jesus spoke quietly. “You mistook love for a command because fear was standing near it.”
Eliab covered his face. He did not weep loudly this time. The tears came with less violence and more surrender, which somehow made him feel younger. Mara reached for him with her good hand, but stopped, unsure whether he would pull away. He saw the hesitation through his fingers and moved toward her before fear could change his mind. She drew him in, awkwardly because of her wrist, and held him as if he were both the boy she had almost lost to hardness and the baby she remembered before grief had a name.
Dalia climbed into the small space beside them, pressing her shoulder into Eliab’s arm. For a while, no one tried to make the moment useful. The lamp had not yet been filled. The jar was still broken. Natan’s mother was still offended. There would still be work, debt, hunger, gossip, and the long uneven labor of living after loss. Yet something in the house had shifted because the sorrow was no longer being forced to wear armor.
When Mara finally released him, Eliab wiped his face and looked at Jesus. “Is this what You wanted?”
Jesus’s expression held no triumph. “I wanted the truth to have room.”
“It hurts.”
“Yes.”
“I thought truth would make me stronger.”
“It will,” Jesus said. “But first it may make you honest.”
Eliab looked at the basket of broken clay. “What do I do about Natan?”
The name changed the air. Mara’s face tightened again. Dalia leaned back. The well returned to them with its staring faces and spilled water.
Jesus did not answer for him. “What do you think you should do?”
“He mocked us.”
“Yes.”
“He should be sorry too.”
“Yes.”
“So why must I go first?”
Jesus looked at him with deep kindness and no escape in His eyes. “Because your wrong belongs to you before his wrong belongs to him.”
Eliab looked down. This was the part he hated. Repentance had seemed almost possible in his own house, held by his mother, softened by Dalia’s song. But Natan was different. Natan would smirk. Joah would laugh. Natan’s mother would look down her nose. The village might hear. Saying the truth at the well had been forced by the moment; choosing it afterward felt like walking willingly into shame.
“I cannot,” Eliab said.
Jesus did not rebuke him. “You can. You do not want to.”
The plainness of it made Eliab angry, but not as sharply as before. “Would You want to?”
“I would want what my Father wants more than what pride protects.”
Eliab stared at Him. There were times when Jesus said Father and the word seemed to hold more than any child’s mouth should hold. It did not sound borrowed from Joseph, though Joseph was good. It sounded like a door opening toward a place Eliab could not see.
“My father would have made me apologize,” Eliab said after a moment.
“Would he have stood beside you?”
The question undid him again, but quietly. “Yes.”
Jesus nodded. “Then let love remember him truthfully. Not as a weight on your shoulders, but as a voice calling you toward what is right.”
Mara touched Eliab’s hair. “I can go with you.”
His pride stirred. Then he looked at her wrist. “No. You should rest.”
“I am still your mother.”
“I know.” He said it differently now, less like resistance and more like gratitude. “But I broke it. I struck him. I should go.”
Dalia whispered, “Will he hit you?”
“No,” Eliab said, though he did not know.
Jesus rose. “I will walk with you if you choose to go.”
Eliab looked toward the doorway. Outside, afternoon light lay across the courtyard. The village beyond it seemed suddenly too large, full of eyes and mouths. He wanted night to come. He wanted Natan to move away forever. He wanted Jesus to say that private sorrow was enough and public obedience could wait.
Instead, Jesus waited.
Mara stood and took the small lamp in her good hand. “Before you go, fill this from the little oil left.”
Eliab looked at her. “We should save it.”
“We have been saving everything until there is no light in us.” She held the lamp toward him. “Fill it.”
He took the lamp, then the small oil flask from the shelf. His hands shook as he poured. There was not much. The oil slid in a narrow line, amber in the dimness, and settled at the bottom. He wanted to apologize for using it, but something in his mother’s face stopped him. This was not waste. It was witness.
Mara lit the wick. A small flame rose, leaned, steadied. Dalia smiled at it. Eliab watched the light gather itself in the repaired place where the shelf had failed.
Jesus looked at the flame, then at Eliab. “A house does not become whole because nothing breaks. It becomes whole when truth and mercy are allowed to live there after the breaking.”
Eliab held those words as carefully as the lamp. They did not solve what came next. They gave him a way to step toward it.
He set the lamp down, wiped his hands on his tunic, and walked to the doorway. Jesus followed. At the threshold, Eliab stopped and looked back. His mother stood beside the repaired shelf. Dalia stood near her, humming again under her breath, not loudly, but without fear. The basket of broken clay remained on the floor. Eliab understood then that the house did not need him to pretend nothing was broken. It needed him to stop breaking more things in the name of protection.
He turned toward the lane. “I will go.”
Jesus walked beside him, not behind this time.
They found Natan near his own courtyard, sitting with his bruised shoulder bare while his mother rubbed it with oil. Joah was there too, eager for whatever might happen next. Eliab felt his courage shrink as soon as Natan saw him. The other boy’s eyes narrowed.
“Come to break another jar?” Natan said.
Eliab stopped. Jesus stood at his side, silent.
Natan’s mother rose. “Why are you here?”
Eliab’s mouth dried. He could feel every path of escape. He could accuse Natan. He could say he was sorry in a way that still blamed the insult. He could look at Jesus and let Him speak. Instead, he forced his eyes to Natan’s face.
“I came because I struck you,” he said. “You mocked my mother, and that was wrong. But I struck you, and that was mine. I am sorry.”
Natan glanced at Joah, then back at Eliab. A smirk began and failed. The apology had not made Eliab small in the way Natan expected. It had made the moment serious.
Natan’s mother folded her arms. “And the jar?”
“I broke it. I cannot replace it now.” Eliab swallowed. “I can work toward it, if you require something for the trouble I caused.”
Jesus’s eyes remained on Natan, not pressing, simply seeing. Natan shifted under that gaze. His bravado thinned. “You swung like a goat kicks.”
Joah laughed weakly. Natan’s mother gave him a warning look, but Jesus did not speak. Eliab stood still. The insult had landed, but it had not found the same door. He felt anger rise and then felt it meet the truth waiting inside him. His wrong belonged to him. Natan’s wrong belonged to Natan. He did not have to carry both.
Natan rubbed his shoulder. “It hurts.”
“I know,” Eliab said.
“You looked foolish.”
“I know.”
Joah frowned, disappointed that the words were not becoming a fight.
Natan looked at Jesus again, then away. His face flushed. “I should not have said her name like that.”
His mother turned sharply toward him. “Natan.”
The boy stared at the ground. “I should not have mocked your mother.”
The apology was rough and unwilling, but it was there. Eliab did not know what to do with it. He had imagined punishment, laughter, maybe a shove. He had not imagined Natan’s shame appearing beside his own.
Jesus spoke for the first time. “Then let the wrong stop here.”
No one answered. The courtyard held the uneasy peace of people who had not become friends but had stepped back from becoming worse enemies. Eliab nodded once. Natan nodded back, barely.
As Eliab and Jesus turned away, Joah muttered something under his breath, but Natan did not laugh. That was not full repentance, not yet. It was enough for the moment.
On the path home, Eliab walked slowly. He looked shaken, but not crushed. “I thought I would feel clean.”
Jesus glanced at him. “What do you feel?”
“Tired.”
“Truth can make room for rest before it makes joy.”
Eliab thought about that. The sun had lowered, and the lane was beginning to soften again. He could see his house ahead, the small lamp glowing inside. For the first time since his father’s death, the light did not look like proof that his mother was working too late. It looked like someone was waiting.
At the courtyard gate, he stopped. “Jesus.”
Jesus turned.
“When I said my father looked like he needed something from me…” Eliab’s voice grew thin. “What if I cannot forget that?”
“Do not try to forget it tonight.”
“What do I do?”
“Ask God to show you the look again without fear standing in front of it.”
Eliab’s eyes moved toward the lamp. “Will He?”
“Yes.”
The answer was not loud, but Eliab believed that Jesus knew. He did not understand how. He only knew that when Jesus spoke of God, the world seemed less abandoned.
Inside, Dalia’s humming had become a song with words again. Mara’s voice joined for one line, tired and unsteady. Eliab stood at the gate and listened. The house was still poor. His mother was still widowed. His father was still gone. But the song had returned to the room, and for that evening, he did not silence it.
Chapter Four
Eliab woke before his mother called him. For a moment, in the gray quiet before morning found the walls, he did not remember everything. He only knew that his face felt tight from tears and that his chest felt strangely hollow, as if something heavy had been removed but the place where it had rested still hurt. Then he heard Dalia breathing near the hearth, heard his mother shift on her mat with a small sound of pain from her wrist, and the day returned to him whole.
The broken jar. The apology. The lamp. The song.
His father.
He lay still and looked toward the shelf Joseph had repaired. The new lamp sat there, unlit now, ordinary in the dimness, but he remembered the way its flame had steadied. Beside the wall, the basket of broken clay waited. Mara had not hidden it. She had placed it where anyone in the house would see it, not to accuse him, he was beginning to understand, but to tell the truth gently enough that they could live with it.
Dalia stirred and opened her eyes. When she saw him awake, she smiled sleepily, then seemed to remember caution. The smile grew smaller.
Eliab whispered, “You can sing when you wake.”
She watched him carefully. “Even if you are counting grain?”
He closed his eyes for a breath. “Even then.”
That seemed to satisfy her. She rolled over and pulled the corner of her blanket to her chin. A few moments later, very softly, she began humming the goat song. It was a ridiculous song, full of little jumps and turns, and Eliab felt the old irritation begin to rise out of habit. But beneath it came another feeling, quieter and truer. He had missed that sound. He had hated it because he had missed it, because it reminded him of the house before the fever, before whispers, before men lowered their voices around his mother. He turned toward the wall until the tears that came did not frighten his sister.
When Mara rose, he fetched water without being told. He moved carefully, not with the frantic speed he had once mistaken for usefulness, but with attention. He swept near the doorway. He checked the strap on Dalia’s sandal. He set aside the last good jar and did not touch it without asking. Mara noticed all of this, and her face held gratitude mixed with grief, because a mother can be thankful for change and still mourn what forced it.
“You are to go to Joseph this morning,” she said after they had eaten.
Eliab nodded.
“Take your father’s tools.”
His hand paused over the bread crumbs. “I thought you wanted them here.”
“I wanted them guarded. That is not the same as used.” She looked toward the corner where the wrapped bundle lay. “Your father did not keep tools so they could become a shrine to what we lost.”
The words unsettled him. He had treated those tools as if touching them wrongly would dishonor the dead. He had also treated them as if they could make him into the dead man’s replacement. Neither had given him peace.
Mara saw his hesitation. “Bring them to Joseph. Let him teach you slowly.”
“I do not want to ruin them.”
“Then learn before you force them.”
Eliab almost smiled. “That sounds like Joseph.”
“It is wisdom. Joseph does not own all of it.”
For the first time in many days, his mother’s voice held a little dry humor. It startled him, and because it startled him, he almost laughed. Dalia did laugh, and the small house received it without flinching.
Eliab wrapped the tools in the cloth and stepped into the lane. Morning had just begun to move. Women were already near the well, but fewer than usual. Smoke rose from ovens, and a man led two goats with the resigned expression of someone losing an argument to animals. Nazareth had not changed, yet Eliab felt as if every stone knew what had happened at the well. He passed the place where the jar had broken and saw a dark mark still faint in the dust. He did not stop. He did not look away either.
Joseph was already working when Eliab arrived. Jesus sat nearby, shaping a small piece of wood with a focus so complete that Eliab felt quieter just seeing Him. The early light touched His face and hands. He looked up before Eliab spoke.
“You came,” Jesus said.
“I said I would.”
“Yes.”
There was no praise in the answer, but there was gladness, and Eliab found he preferred that. Praise would have made him feel watched. Gladness let him stand.
Joseph took the bundle and opened it on the workbench. He lifted the chisel first, then the adze, then a small measuring cord Eliab had forgotten was wrapped inside. The cord had knots darkened by years of use. Joseph held it with care.
“Your father kept good tools,” he said.
Eliab’s throat tightened. “He said he would teach me to fit a door before winter.”
Joseph looked toward him. “Then we will begin with a door.”
Fear moved quickly through Eliab. “Now?”
“Not a house door. A small storage door. Your mother’s back niche has never sat square. Your father meant to mend it. I remember him saying so.” Joseph lifted the chisel. “We will not finish because you are ready to prove something. We will finish if the work becomes true.”
Eliab looked at Jesus. “Did You tell him about that?”
Jesus shook His head. “No.”
“Then how did he know?”
Joseph smiled faintly. “Your father and I spoke of more than plow beams.”
The answer opened a door Eliab had not known was there. His father had talked about the house’s needs with another man. He had planned, hoped, noticed, intended. His death had not erased those intentions. They had simply fallen into the hands of people still living.
Joseph sharpened the chisel first. He did not let Eliab do it alone. He showed him the angle, the pressure, the patience of passing edge across stone. Eliab wanted to hurry. Joseph stopped him each time.
“Listen to the sound,” Joseph said. “A tool tells you when you are forcing it.”
Eliab tried again. The scrape changed when his hand steadied. Jesus watched without interrupting. After a while, Joseph gave Eliab a scrap of wood and asked him to pare one thin shaving. Eliab pressed too hard. The chisel dug and split the piece.
Heat rose in his face. “I ruined it.”
“You ruined a scrap,” Joseph said. “That is what scraps are for.”
Eliab stared at the split wood. The old pressure surged. He wanted to throw the piece down. He wanted to say he could not learn this way. He wanted to turn fear into anger because anger felt stronger than embarrassment. His fingers tightened.
Jesus stood and came near. “What are you hearing inside?”
Eliab did not want to answer. “Nothing.”
Jesus waited.
The boy swallowed. “That I am too late.”
Joseph set the sharpening stone down.
Eliab hated that he had said it, but now the words kept coming. “Too late to learn. Too late to help. Too late to be what he needed. Everyone else knows things. Men know how to fix shelves and yokes and doors. I know how to break jars.”
Jesus looked at him with such steady compassion that Eliab could not hide in bitterness. “You are not too late to become a son again.”
Eliab’s eyes burned. “I do not know how to be that.”
“Begin by not punishing yourself for being unable to be a father.”
Joseph’s face softened, but he remained quiet. This work, Eliab understood, was not only happening on the bench.
They went to Mara’s house after the sun cleared the roofs. Joseph carried the main tools, Eliab carried his father’s bundle, and Jesus carried two pieces of planed wood. Mara had cleared the back niche. It was a small opening in the wall where grain sacks and mending bundles were kept, covered by a rough wooden door that scraped at the bottom and left a gap near the top. Dalia hovered nearby, curious but under strict warning not to touch any blade.
Joseph removed the door and set it on two low supports in the courtyard. “See here,” he said to Eliab, guiding his hand along the edge. “The wood swelled, then dried unevenly. If you cut from fear, you will take too much. If you refuse to cut, it will never fit. Wisdom is not doing nothing. Wisdom is removing what keeps the door from closing true.”
Eliab ran his fingers along the warped edge. The lesson was too plain to miss, but Joseph did not press it into a sermon. He simply handed him the marked place and stood close.
The first shavings came badly. Eliab’s hand shook. Joseph adjusted his grip. Jesus steadied the board. Dalia hummed behind them, forgot herself, and began singing louder. Eliab’s shoulders tightened. The chisel slipped and made a crooked bite.
“Dalia,” he snapped.
The song stopped. The courtyard froze.
Eliab closed his eyes. There it was again. Not as violent as the well, not as loud as the broken jar, but the same fear using his mouth. He opened his eyes and saw his sister’s face fall.
He set the chisel down.
Mara watched from the doorway, holding her wrapped wrist. Joseph did not rescue him. Jesus did not soften the moment. Eliab had asked what to do, and life had given him a smaller, truer place to do it.
“I am sorry,” he said to Dalia.
She looked at him carefully. “I was not touching the tool.”
“I know. I was angry because I made a bad cut.”
“Will the door be ruined?”
Eliab looked at Joseph. Joseph shook his head once.
“No,” Eliab said. “But I spoke like it was your fault.”
Dalia nodded, satisfied by truth more quickly than adults usually are. “Can I sing softer?”
Eliab breathed out. “Yes. And if it bothers me, I will say it kindly.”
Dalia resumed, softer at first. The work continued. Something in Eliab loosened, not because he had become patient all at once, but because he had stopped needing failure to find someone else to blame. The shavings grew thinner. The edge began to straighten. Joseph let him make the next mark. Jesus held the door steady, His young hands firm against the wood, and Eliab saw again the strange wonder of Him. Jesus did not make the work easier by removing the difficulty. He made it possible to remain truthful inside it.
Near midday, they set the door back into the niche. It still scraped.
Eliab’s face fell. “After all that?”
Joseph opened it, closed it, then opened it again. “Better than before. Not true yet.”
The words struck the place where Eliab wanted every effort to become instant proof. He stared at the door, tired and frustrated. Mara looked as if she might say they could finish another time, but Jesus spoke before she did.
“What do you want to do?”
Eliab knew the answer that fear wanted. Quit before the work proved him small. Blame the wood. Blame the old wall. Blame the song. Blame his dead father for leaving the task unfinished. Blame God because the world had become too heavy for a boy.
He gripped the door edge. “Try again.”
They removed it. This time Joseph let Eliab find the place that caught. It took him longer than he wanted, but he found it. He marked it lightly. He shaved carefully, stopped, tested, shaved again. Dalia’s song wandered in and out of words. Mara sat in the shade, tears in her eyes that did not seem only sad. Jesus watched the door and the boy, and the courtyard seemed to hold its breath.
When they set the door again, it closed. Not perfectly. It still rubbed faintly, but it closed without force, and the gap at the top was smaller. Eliab stood looking at it as if he had expected the heavens to open or his father’s voice to speak from the wall. Instead, the door simply fit better than it had. That was all. That was enough.
Mara came forward and touched the wood with her good hand. “Your father would have been glad.”
Eliab’s face crumpled. He turned away, but not to hide this time. He turned because the words had entered him too deeply for his face to hold. “I thought he was disappointed in me.”
Mara came closer. “No.”
“I thought when he looked at me, he knew I could not do it. I thought he was leaving it all to me because I was supposed to become enough. I thought God saw I was not enough and took him anyway.” His voice broke, but he kept going because this was the thing under all the other things, the dark root that had fed his fear. “I thought if I became hard enough, maybe it would make up for being small when he needed me.”
The courtyard went utterly still. Even Dalia stopped singing.
Jesus stepped toward him. His face was tender and grave. “Your Father in heaven did not ask you to pay for being a child.”
The words struck with such force that Eliab bent as if under a weight leaving him too quickly. Mara reached for him. Joseph looked down, his own eyes wet. Dalia began crying without fully understanding why.
Jesus continued, and His voice was quiet but seemed to fill the courtyard. “You were not measured and found too small. You were loved while you were small. You are loved still. The burden you have carried was never given by God.”
Eliab sank to his knees beside the little door. He pressed both hands over his face, and this time he did not try to control the sound that came from him. It was grief, repentance, relief, and the first fragile breath of a child who had been allowed to stop pretending. Mara knelt despite her wrist and held him. Dalia wrapped her arms around both of them. Joseph turned his face away for a moment, giving them the dignity of not being watched too closely.
Jesus knelt near them, not intruding, not distant. The fitted door stood behind them, imperfect and closed, a small witness in a poor courtyard that something could be corrected without being made flawless, that love could finish what fear had left unfinished, and that a son did not have to become his father in order to honor him.
When the weeping quieted, Eliab lowered his hands. His face was wet and open in a way Jesus had not seen before. “What do I do now?”
Jesus looked at the door, then back at him. “You live as a son. You learn slowly. You tell the truth sooner. You let songs remain in the house. And when fear says you must become hard to keep love safe, you remember this day.”
Eliab nodded, though he knew remembering would not be simple. Fear would return. Shame would speak again. Work would still be needed. Food would still be counted. But the false command had been named, and once a lie is brought fully into the light, it may still whisper, but it no longer owns the room in the same way.
That evening, after Joseph and Jesus returned home, Eliab lit the small lamp on the repaired shelf. Dalia sang while Mara mended with her injured wrist resting more often than before. The new-fitted door stood closed at the back niche. Eliab did not feel like a man. He felt tired, sad, and strangely young.
For the first time in a long while, that did not seem like failure.
Chapter Five
By the next morning, Nazareth knew a version of what had happened. Small villages had a way of carrying stories faster than water from the well, and no story ever arrived unchanged. Some said Eliab had struck Natan because of a cruel word. Some said the widow’s son had finally become wild from grief. Some said Jesus had stood between them with such calm that the boys forgot how to keep mocking. Some were kinder. Some were not. By the time the sun rose over the low roofs, Eliab could feel the village looking at him before he stepped outside.
He wanted to stay inside. The wish came strongly enough that he almost obeyed it. The small door at the back niche now closed with only a faint rub, the lamp sat clean on the repaired shelf, and Dalia had begun the morning by singing while Mara braided her hair. For one brief hour, the house felt like a place where healing might remain private. Then Mara asked him to carry a mended garment back to Tirzah near the well, and the ordinary world required him again.
Eliab held the folded garment under one arm and stood in the doorway. “Can it wait?”
Mara looked up from sorting thread. She did not shame him with a quick answer. Her wrist was still wrapped, though the swelling had gone down some, and she moved it carefully when she worked. “It could wait,” she said, “but I do not think waiting will make the lane easier.”
Dalia looked at him from the floor. “I can come.”
“No,” Eliab said too quickly, then softened when she flinched. “Not because of you. I just need to go.”
Mara’s face held the quiet pride of a mother watching a child choose something difficult for the right reason. “Then go, and come back by the lower path if the well is crowded.”
Eliab almost accepted the escape before she finished speaking. Then he thought of Jesus asking what he was hearing inside. He listened, and what he heard was fear trying to sound like wisdom. “I will take the well path.”
Mara nodded. She did not praise him. She simply let the choice stand.
Outside, the morning was bright and dry. A few children chased one another around a low wall until a woman called them back to their chores. A man Eliab barely knew gave him a look that tried to be sympathetic and only made him feel studied. Eliab kept walking. His steps slowed near the place where the jar had broken. The mark in the dust had faded, but his memory of it had not. He saw again the water spreading, Dalia crying, Natan holding his shoulder, and Jesus standing close enough to keep him from more sin.
At the well, Tirzah was not alone. Natan’s mother stood there with two other women, and Natan himself sat on the stones with Joah nearby. Eliab’s first thought was that he should have taken the lower path. His second thought was that turning back would be its own kind of obedience to fear. He gripped the garment and continued.
The women saw him. Their talk thinned at once. Natan looked away, then back, then down at the dust. Joah watched with open interest, hoping perhaps for another scene to carry through the village. Eliab felt anger stir at that look. He also felt shame, but it no longer had the same command in it. Shame told him to defend himself before anyone spoke. Truth told him to deliver the garment.
He went to Tirzah and held it out. “My mother finished the mending.”
Tirzah took the garment, unfolding one corner to inspect the seam. Her eyes warmed. “Her stitches are clean even with a hurt wrist.”
“I will tell her you said so.”
Natan’s mother spoke before he could leave. “Is your mother’s wrist healing?”
The question surprised him. It did not sound like mockery. It sounded like someone unsure how to step around yesterday without pretending it had not happened.
“It is better,” Eliab said. “Still sore.”
She looked toward Natan, then back at Eliab. “My son’s shoulder is bruised but not badly.”
Eliab nodded. “I am glad it was not worse.”
Natan shifted on the stones. Joah nudged him with an elbow, expecting some sharp reply. Natan did not give one. He kept his eyes on the ground and muttered, “It still hurts.”
Eliab felt the old reply rise. Good. Then he felt, beneath it, the memory of Dalia’s fear and his mother gathering broken clay. He drew a breath. “I am sorry for that.”
Natan looked up. For a moment, both boys seemed caught in the awkwardness of mercy after anger. They had no friendship to return to, no easy laughter waiting underneath. They only had a narrow place where something worse did not have to grow.
Joah frowned, annoyed by the quiet. “You both sound like old women at mourning.”
Natan glanced at him, and Eliab felt the whole moment lean. There it was, the test that did not announce itself as a test. Natan could laugh, and the cruelty would begin again. Eliab could strike back with words, and the old road would reopen. The women watched without seeming to watch. Tirzah folded the garment slowly.
Natan rubbed his bruised shoulder. “Leave it, Joah.”
Joah blinked. “What?”
“I said leave it.”
The words were not noble or grand. Natan still sounded irritated. But he had refused the easy cruelty, and Eliab recognized how hard that could be. He gave Natan a small nod. Natan returned it with the quick discomfort of a boy who did not want anyone to see him becoming better.
Eliab turned to go, then stopped. He looked at Natan’s mother. “My mother has the pieces of the jar. She says we will keep them so we remember what anger costs.”
The woman’s face changed. Tirzah looked down, hiding a faint smile that was not amusement but recognition. Natan’s mother drew her shawl closer around her shoulders. “That is a hard lesson.”
“Yes,” Eliab said. “But it is helping.”
He left before the moment could become more than he had strength to carry. As he walked home, he saw Jesus near Joseph’s work area, carrying a narrow board across His shoulder. Jesus did not call out. He only looked at him, and Eliab knew He had seen enough to understand.
Later that day, Joseph came to Mara’s courtyard to check the door once more and bring a small piece of wood for the threshold. Jesus came with him. Eliab expected more instruction, but Joseph simply set him to work with the measuring cord, guiding him when needed, letting him make slow choices. Dalia sat nearby with a scrap of thread, trying to copy her mother’s stitches in a piece of old cloth. Mara rested more often, which was itself a kind of obedience for her. Every time she paused without apologizing, Eliab noticed.
The work was small. That was what made it holy in a way Eliab had not expected. No one watching from outside would have thought anything great was happening. A poor courtyard. A boy learning to measure. A carpenter adjusting a threshold. A ten-year-old Jesus holding wood steady while a little girl sang a goat song badly and with confidence. Yet Eliab felt the change more deeply than he had felt the public apology. He was not being asked to save the house. He was being allowed to belong to it.
At one point, the threshold piece shifted, and Eliab made a mark too short. He noticed after the cut began. His stomach tightened. Joseph saw it too.
“What do you do when a mark is wrong?” Joseph asked.
Eliab closed his eyes for a moment. The old answer would have been to hide it, rush past it, blame the cord, or press harder until the mistake became damage. He opened his eyes and set down the tool. “I say it is wrong before I make the cut worse.”
Joseph’s smile was small but real. “Good.”
Jesus looked at Eliab, and there was gladness in His face again. Eliab felt it settle in him like water after thirst. Not praise for perfection. Gladness for truth.
By evening, the threshold sat better. The door still was not perfect, but it opened and closed with a sound that no longer made Mara wince. Joseph gathered the tools, and Eliab wrapped his father’s chisel carefully. For the first time, he did not feel as if the cloth were covering a command. It was holding a gift.
Mara brought bread to the courtyard. It was not much, and she looked briefly embarrassed by how little there was. Mary had come near the gate with a small jar of oil and a few olives, and when Mara saw her, the old pride rose again in the quick lift of her chin. Eliab watched it happen. He also saw his mother’s weariness underneath.
Mary did not step in as if delivering rescue. She held the jar out quietly. “I had more than I needed today.”
Mara looked at the oil. The whole courtyard seemed to wait. Eliab understood then that his mother had her own false belief, not the same as his but close enough to wound the same house. She believed receiving too much would make her less honorable, less capable, less herself. He wanted to tell her to take it. He wanted to spare her the struggle. But Jesus had not spared him truth, and he knew love sometimes waited while another person chose.
Mara’s eyes filled. She reached for the jar with her good hand. “Thank you.”
Mary stepped forward and touched her arm. “Peace to this house.”
Mara nodded, unable to answer for a moment. Dalia, sensing permission where adults felt gravity, began singing again. This time no one stopped her. Her small voice wove through the courtyard, imperfect and bright, moving around broken clay, repaired wood, tired hands, and faces still learning how to live honestly.
Eliab looked at Jesus. “Will fear leave now?”
Jesus stood near the gate, the last light of evening resting along His hair and shoulders. “It may come back tomorrow.”
The answer disappointed him, though he had known it would be true.
Jesus continued, “But now you know its voice. You do not have to call it love when it speaks. You do not have to call it duty when it makes you cruel. You do not have to call it strength when it forbids you to grieve.”
Eliab looked toward the basket of broken clay. “And if I forget?”
“Then tell the truth again.”
“That sounds like a lifetime.”
Jesus looked at him with a depth that made Eliab feel seen beyond the years he had lived. “Yes.”
The word did not frighten him as much as it might have before. A lifetime of truth sounded hard, but a lifetime of hiding had already begun to destroy him. He looked at his mother receiving oil without apology, at Dalia singing without fear, at Joseph standing beside the tools, at Mary smiling with tears in her eyes, and he understood that healing was not the removal of everything painful. It was the presence of God in the place where pain had stopped being hidden.
After the meal, Eliab carried the basket of broken jar pieces to the repaired shelf. Mara watched him but did not stop him. He placed the basket beneath the new lamp, not in the way a criminal keeps evidence, but in the way a household keeps memory. The broken pieces would remain there for a season. Perhaps one day they would be ground into clay for some lesser use, or buried near the wall, or scattered in the path where feet would press them into dust. For now, they belonged in sight.
He lit the lamp. The flame rose and steadied.
Mara came beside him. “Your father loved you,” she said.
Eliab did not answer at once. He looked at the flame until it blurred. “I know.”
It was the first time he had said it without arguing with the memory. Mara put her arm around him, and he leaned into her carefully so he would not hurt her wrist. Dalia pushed herself between them because she refused to be left outside any embrace that happened in her own house. Eliab laughed, and the sound surprised him. It had sadness in it, but sadness was not the only thing there.
When Jesus and His family left, the sky was already darkening toward night. Eliab followed them to the gate.
“Jesus,” he said.
Jesus turned.
“I think when my father looked at me, he was saying goodbye.”
Jesus’s face grew tender. “And love.”
Eliab nodded slowly. “And love.”
Jesus did not add more. The truth had landed. Words beyond it would only crowd the room God had made.
The days that followed did not become easy. Mara still worked too late sometimes, though now she let Mary or Tirzah sit with her when the lamp burned low. Eliab still felt anger rise when boys laughed near the well, and more than once he had to walk away before his mouth made trouble for his heart. Natan did not become a close friend, but he stopped speaking Mara’s name with contempt, and Joah learned that mockery was less amusing when no one fed it. Dalia sang loudly when she forgot herself, softly when Mara’s head hurt, and often enough that the house no longer felt afraid of music.
Eliab went to Joseph three mornings each week. He swept, carried, watched, asked, and made mistakes on scraps that taught him without destroying what mattered. Jesus was often there, sometimes speaking, sometimes simply working nearby in silence. Eliab began to understand that silence could be full of peace rather than fear. He began, slowly, to pray with words that did not sound borrowed. At first he told God he was angry. Then he told God he was tired. One morning, without planning to, he thanked Him for his father’s hands, his mother’s strength, his sister’s song, Joseph’s patience, Mary’s kindness, and the strange mercy of Jesus, who had not let him hide behind grief.
On the final morning of that season, before Nazareth woke fully, Jesus returned to the quiet place where the story had begun. The earth was cool beneath Him. The sky held the first pale promise of dawn. In the distance, a lamp still burned in Mara’s house, but now it did not burn as a sign of a widow working herself past strength. It burned because Eliab had risen early to fill it before going to learn, because Dalia had woken singing, because Mara had smiled and told them both to let the morning come gently.
Jesus knelt and opened His hands before His Father. He prayed for Eliab, still tender where the false burden had been lifted. He prayed for Mara, learning to receive without shame. He prayed for Dalia, whose songs had survived the silence. He prayed for Natan, who had taken one small step away from cruelty. He prayed for Joseph and Mary, whose ordinary faithfulness had made room for mercy to become visible. And as Nazareth woke under the same old pressures, the Son remained in quiet prayer, holding the hidden wounds of a small village before the Father who had seen every one.
Your friend, Douglas Vandergraph
Watch Douglas Vandergraph inspiring faith-based videos on YouTube: https://www.youtube.com/@douglasvandergraph
Support the continued growth of the Douglas Vandergraph Christian encouragement library: https://www.buymeacoffee.com/douglasvandergraph
Back from America's West Coast
from 3c0
I’m back from the best coast. The dreamiest coast. California is special. I would visit the Bay Area as a kid.
At least 3 relatives on my mother’s side of the family lived there until their deaths. Even my mother resides there now. I learned that we could’ve easily been American citizens before she married our father, but she decided against it.
This trip reminded me why they wrote all those songs about it. Joni’s California.
Sadly, they still won’t give peace a chance, even today in 2026.
Minimalism Is Not Neutral: The Hidden Power Behind Less
from  SmarterArticles
SmarterArticles

In 2016, Kyle Chayka, then a freelance culture writer and now a staff writer at The New Yorker, published an essay in The Verge that put words to a feeling millions of travellers had but could not quite articulate. He called it “AirSpace”: the creeping sameness of coffee shops, co-working offices, hotel lobbies, and Airbnb listings across the globe, all converging on the same reclaimed wood, Edison bulbs, industrial lighting, and Scandinavian-adjacent minimalist furniture. “The homogeneity of these spaces means that traveling between them is frictionless,” Chayka wrote, “a value that Silicon Valley prizes.” You could land in Lisbon, Seoul, or Mexico City and find yourself in an interior indistinguishable from a Brooklyn cafe. The aesthetic was not accidental. It was algorithmic.
Eight years later, Chayka expanded the argument into a full book, Filterworld: How Algorithms Flattened Culture (Doubleday, 2024), documenting how algorithmic recommendation systems had not merely homogenised digital feeds but reshaped the physical world in their image. The thesis was stark: platforms like Instagram, Airbnb, TikTok, and Spotify had produced “a world of averages: ideas and aesthetics optimised for engagement that are as acceptable as possible to as many people as possible.” Minimalism, once a deliberate philosophical stance against consumer excess, had calcified into the default setting of a globalised attention economy. And the people who benefited most from this flattening were not the communities living inside these spaces but the platform operators, venture capitalists, and design consultancies who had quietly claimed the authority to define what “essential” means.
This is an article about that authority. Not about whether minimalism is beautiful (it often is) or whether it improves usability (it frequently does), but about who profits when a design philosophy hardens into an unexamined assumption, and what disappears when every surface on earth is stripped to elements deemed “essential” by a remarkably small group of decision-makers.
The Branding Agencies That Built a Monoculture
If you purchased a direct-to-consumer product between 2012 and 2020, the odds are good that its branding was designed by one of two Brooklyn-based agencies: Red Antler or Gin Lane. Red Antler designed the branding for Casper, Allbirds, Birchbox, and Hinge. Gin Lane built brand identities for Sweetgreen, Harry's, and Everlane. Between them, these two firms defined the visual language of an entire generation of venture-capital-funded consumer startups: sans-serif typography, pastel colour palettes, generous white space, whimsical line illustrations, and recycled cardboard packaging that communicated both premium quality and environmental virtue.
The result, as a 2021 Retail Dive investigation documented, was a “distinct digitally native aesthetic being adopted by many of these leading brands, likely as a result of an incestuous agency relationship.” The formula was remarkably consistent. A catchy, memorable name. A poppy accent colour. Hyper-designed packaging. And a tone of voice that Glossy described as the “Hey, girl” register of Glossier, which influenced countless brands including larger competitors like Estee Lauder.
The economic logic was straightforward. Partnering with Red Antler or Gin Lane could cost a brand up to $400,000 in branding alone, with additional PR costs of $180,000 to $240,000 per year. But the investment paid off, because the aesthetic itself functioned as a signal. Alex Song, founder and CEO of the Innovation Department, explained that it was “really easy for me to just engage the Red Antlers, the Gin Lanes, all the branding businesses that built the initial winners.” Adopting the now-familiar branding themes could signal to consumers that the company was part of the set of brands they already trusted.
This created a feedback loop with no obvious exit. Venture capital firms funded DTC startups. Those startups hired the same small cluster of agencies. Those agencies produced visually similar brands. Consumers learned to associate that visual similarity with trustworthiness. New startups then had to adopt the same look to be taken seriously. As Zak Normandin, founder of Iris Nova, told Modern Retail: “Entrepreneurs have been misguided in this idea that if you just well-design a consumer product and put a different branding spin on it, then that's enough for a formula to build a really big business.” The monopoly was not merely aesthetic; it was structural, with design firms and agencies concentrating power over what a “modern” brand should look like.
As the DTC space grew more competitive, even Red Antler found itself in an unusual position: having to differentiate its new clients from the very aesthetic template it had helped create. Red Antler co-founder and CEO JB Osborne told Adweek that larger consumer brands were “catching up and they're launching businesses that are mimicking the direct consumer model, but more importantly, the direct consumer aesthetic.” The copiers were being copied. The monoculture had become self-replicating.
The Sans-Serif Invasion and the Death of Distinction
The homogenisation extended well beyond DTC startups. Beginning around 2017, a wave of established brands, from fashion houses to technology companies, abandoned their distinctive logos in favour of nearly identical sans-serif wordmarks. Developer Radek Sienkiewicz, writing on his site VelvetShark, identified the pattern with precision: “It's as if many companies decided that being unique was a handicap and that it was better to be like everyone else.”
The list of casualties is long. Burberry, Balenciaga, Celine, Calvin Klein, Diane Von Furstenberg, Saint Laurent, Rimowa, Balmain; all underwent rebrands that replaced distinctive, heritage-laden typography with clean, geometric sans-serif fonts. Technology companies followed. Google, Spotify, Airbnb, and Pinterest gravitated toward simple lowercase wordmarks. As Sienkiewicz observed, “It looked like two huge industries decided to use the services of one designer, and not a particularly inventive one at that.”
The Burberry case is particularly instructive. In 2018, the British luxury house commissioned graphic designer Peter Saville and then-creative director Riccardo Tisci to redesign its visual identity. The result replaced the Equestrian Knight logo, which had served the brand since 1901, with a clean sans-serif wordmark and a “TB” monogram. The redesign drew immediate criticism for erasing over a century of visual heritage. Then, in 2023, under new creative director Daniel Lee, Burberry reversed course entirely, reviving the 1901 Equestrian Knight motif in a bold electric blue and returning to a serif typeface that referenced the brand's archival typography. Saville himself called the reversal “totally and utterly irresponsible” in a 2025 Dezeen interview, not because the new design was poor but because it created a period in which, as he put it, customers could find “three different Burberrys” in the world. The episode illustrated something important: minimalist rebranding is not a neutral act of modernisation. It is a bet that the future will reward sameness over heritage, and that bet does not always pay.
The phenomenon acquired a name: “blanding.” Legal experts at the intellectual property firm Boult warned that this “increasing trend of brands adopting similar, generic identities contradicts the very purpose of a trademark: to stand out.” Nadine Chahine, a Lebanese type designer who serves as CEO of I Love Typography and director of ArabicType, addressed the crisis at a D&AD panel in London. “There's a lot of [visual] variation at startup stage,” she said, “but more recently they've been homogenised into a very similar look.” Her concern was not merely commercial but cultural: “Some of these brands are very old and are part of the heritage of a country. That heritage is important because it tells the story of how these brands came to be and what they represented.”
Astrid Stavro, Vice President Creative Director at Collins, one of the world's most influential brand consultancies, put it more bluntly at the same event: “In stripping [brand elements] of the things that make them unique, we're stripping them of their soul and heart.”
The explanations for why this happened are themselves revealing about power. Writer and podcaster David Perell, whose Twitter thread on the subject gathered 250,000 likes and 50,000 shares, offered two theories: designers are all using the same software, and aesthetic diversity inevitably falls in a hyper-connected world. Matt Johnson, a professor of psychology and marketing at Hult International Business School and an instructor at Harvard, pointed to the “fluency effect,” the behavioural science finding that fonts processed more easily are perceived as more likeable and trustworthy. In a digital environment where consumer attention is strained, legibility becomes the overriding priority. But whose legibility? Legibility for whom? And at what cost?
The Platform as Taste-Maker
The most powerful force driving aesthetic homogenisation is not any single agency or designer but the platform economy itself. Instagram, Airbnb, TikTok, and Pinterest do not merely display aesthetics; they reward certain aesthetics over others, creating feedback loops that shape physical spaces, products, and identities at global scale.
Consider the “AirSpace” phenomenon Chayka identified. In 2011, designer Laurel Schwulst began perusing Airbnb listings across the world, viewing the platform “almost as Google Street View for inside homes.” She noticed a creeping sameness: “The Airbnb experience is supposed to be about real people and authenticity,” she said, “but so many of them were similar,” whether in Brooklyn, Osaka, Rio de Janeiro, Seoul, or Santiago. The listings converged on mass-produced but tasteful furniture, neutral palettes, and clean lines.
This was not coincidence. It was optimisation. Hosts furnish for the algorithm, using pre-made mood boards from Canva, Pinterest, or design blogs. The goal, as nss magazine documented in its 2024 analysis of the AirSpace aesthetic's decline, “is no longer to tell a story about the area, but to avoid annoying the guest.” Posts with the AirSpace look now receive 26 per cent less engagement than in 2020. Hashtags like #airbnbstyle have dropped by 41 per cent in two years, whilst hashtags like #eclectichomes (up 74 per cent), #realhome (up 59 per cent), and #antidesign (up 38 per cent) are rising sharply.
But the damage has been structural. As a 2016 LSE sociology blog post argued, drawing on Pierre Bourdieu's foundational work on taste and social class, the problem with AirSpace “is not homogeneity per se, but that it surfaces as a symptom of the very powerful interplay of aesthetics, design, and politics.” When platforms reward a specific aesthetic, they effectively tax deviation. Hosts, restaurateurs, and shop owners who refuse the minimalist template risk lower visibility, fewer bookings, and reduced income. The platform becomes a taste-maker with enforcement mechanisms built into its recommendation algorithms.
The logic extends beyond interior design. Chayka's Filterworld demonstrated that algorithmic feeds have restructured culture itself. “Algorithmic feeds have utterly taken over both how we create and consume culture,” he wrote. Visual artists must succeed on Instagram to sell their work. Musicians must tailor their songwriting to TikTok to reach audiences. The rule of culture in Filterworld is “go viral or die.” Taylor Lorenz, the journalist and author, praised Chayka's book as “a vital interrogation of algorithmic technology and its unrelenting power in shaping both our online and offline experiences.” Meghan O'Gieblyn, writing for The Atlantic, observed that Chayka demonstrated “how mass culture, even as it diffuses into niche datastreams, trends toward a vacuous mean.” The net result is not a diverse marketplace of aesthetic choices but a convergence on whatever the algorithm rewards, which is invariably content that is smooth, inoffensive, and optimised for the widest possible engagement.
The companies most responsible for this convergence are, as Chayka noted, disproportionately funded by a small cohort of Silicon Valley venture capitalists. The aesthetics they promote are not neutral expressions of universal taste but specific cultural products of a particular class fraction: young, affluent, coastal, technology-adjacent professionals whose preferences have been amplified into a global default by the platforms they built and funded.
The Economics of Erasure
The economic forces propelling minimalist homogenisation are not subtle. They operate at every level, from manufacturing to marketing to global market expansion.
At the manufacturing level, minimalism reduces complexity. Fewer design elements mean lower production costs, simpler tooling, and faster iteration. Apple's minimalist hardware strategy is not merely aesthetic; it is fundamental to the company's business model of producing products that recall each other and prime users to want the next iteration. The financial success of this approach, measured in trillions of dollars of market capitalisation, established minimalism as aspirational. Every competitor rushed to follow.
At the marketing level, minimalism scales. A stripped-down visual identity translates across languages, cultures, and platforms with minimal adaptation. This is enormously valuable for companies seeking global reach. As technology spreads across diverse socioeconomic groups, age ranges, education levels, and literacy levels, designing for maximum diversity forces simplification. The economic imperative to reach the broadest possible market naturally pushes companies toward similar, stripped-down design solutions.
At the macroeconomic level, austerity itself has become a market force. Inflation rates across the United States and Europe hovered between five and seven per cent annually from 2021 onward, eroding disposable incomes and forcing consumers to reassess spending habits. The IMF reported a 3.1 per cent slowdown in global GDP growth projections for 2025. Seventy per cent of consumers reported cutting back on non-essentials, a phenomenon dubbed “the Great Cancellation.” In this environment, minimalism functions not as a philosophical choice but as an economic rationalisation: fewer features, simpler packaging, reduced material costs, all presented as design sophistication rather than cost-cutting.
The global minimalist lifestyle products market, valued at USD 10 billion in 2024, is projected to expand at a compound annual growth rate of 10 per cent, reaching USD 25 billion by 2032, according to FutureDataStats. Minimalism is not merely an aesthetic; it is an industry. And like any industry, it has incumbents, gatekeepers, and profit motives that may diverge sharply from the interests of the communities whose environments it reshapes.
The DTC bubble offers a cautionary tale about where those profit motives lead. For nearly a decade, venture capital firms bankrolled consumer product companies in hopes of exponential growth. But as Matthew Tingler, managing director at investment bank Baird, told Business of Fashion: “Venture capital has soured on consumer product businesses, particularly DTC apparel and footwear.” Capital is shifting from brands to scalable ecommerce infrastructure, platforms, and SaaS. The aesthetic playbook that defined a decade of consumer products is already being abandoned by the investors who funded it. The visual sameness remains, however, in the thousands of brands still operating within the template those investors and agencies created.
Colonial Aesthetics and the Standardisation of Space
The most uncomfortable dimension of minimalism's dominance is its relationship to colonial histories of standardisation and erasure. In August 2025, Celine Semaan, a Lebanese-Canadian designer and founder of the non-profit education platform Slow Factory, published an opinion piece in Dezeen arguing that “minimalist design trends draw from colonial aesthetics that erased cultural specificity, texture, and tradition in favour of uniformity and control.”
Semaan's argument was historically grounded. “Design under empire was not just about making objects,” she wrote. “It was about asserting control and access over resources. Typography, infrastructure, textiles, and architecture were all weaponised to dominate space, erase or discredit Indigenous knowledge systems, and enforce new economic orders.” She pointed to a material reality: trade routes for the materials on which design continues to depend (wood, leather, metals, silks) map identically to colonial routes, reinforcing “the obvious: colonialism is not a thing of the past, it is an ongoing economic reality.” Semaan, who coined the term “fashion activism” and whose first book, A Woman Is a School, was published in 2024, argued that the standardisation and modularity now celebrated as neutral design values were themselves products of colonial logic.
This analysis has been deepened by scholars and practitioners working at the intersection of design and decolonisation. Elizabeth (Dori) Tunstall, an award-winning design anthropologist who served as the first Black person to hold the position of dean of a faculty of design at OCAD University, published Decolonizing Design: A Cultural Justice Guidebook through MIT Press in 2023. Tunstall argued that “from the excesses of world expositions to myths of better living through technology, modernist design, in its European-based guises, has excluded and oppressed the very people whose lands and lives it reshaped.” The book was named to Fast Company's “7 design books to look forward to in 2023,” and The New York Times Book Review noted that “Tunstall gives step-by-step instructions for reducing bigotry's impact on the built environment.” Kevin Bethune called it “a critical addition to the canon of design.”
Julia Watson, an Australian-born designer and educator at Harvard and Columbia, took the argument further in Lo-TEK: Design by Radical Indigenism (Taschen, 2019), documenting traditional ecological knowledge systems from 18 countries, with a foreword by anthropologist Wade Davis. Watson demonstrated that Indigenous communities are “pioneers of technologies that offer solutions to climate change,” challenging the assumption that ancestral design methods are primitive. Her framework proposed that urban design should follow “form follows flux” rather than “form follows function,” prioritising adaptability to dynamic environmental and cultural contexts rather than the static legibility that minimalism demands. Lo-TEK documented systems including living root bridges built by the Khasi tribe in India, floating farms in wetland regions, and the Totora reed floating islands of Peru: complex, adaptive technologies that have sustained communities for centuries but that minimalist paradigms would classify as cluttered or disorganised.
A 2025 paper in the International Journal for Multidisciplinary Research documented how vernacular architectural traditions worldwide are being displaced: “During colonization, indigenous architectural practices were often suppressed or replaced with the styles of the colonizing powers, while the Industrial Revolution introduced mass-produced materials and standardised construction methods.” Today, this shift is “fueled by socio-economic aspirations, with modern architecture symbolising progress and global connectivity. Urban skylines increasingly reflect a universal language of design, often overshadowing the distinctiveness of vernacular traditions.”
The point is not that minimalism is inherently colonial. It is that the universalising impulse behind minimalist design, the insistence that stripped-down forms are inherently superior to ornamental ones, carries forward a logic of standardisation that has historically served powerful centres at the expense of peripheral cultures. When a Nongo basket in South Africa is “reimagined as art” within a minimalist interior, or when Haida prints are “emblazoned” on minimalist silhouettes at Native Fashion Week, the question of who holds interpretive authority over these traditions is never far from the surface.
The Algorithm as Designer
Perhaps the most significant shift in the political economy of minimalism is the transfer of design authority from human communities to algorithmic systems. This is not a metaphor. It is a structural transformation in how aesthetic decisions are made, by whom, and in whose interests.
A 2019 study by Verena Bader and Stephan Kaiser, published in the journal Organization, examined how artificial intelligence was reshaping decision-making processes within organisations. Their findings were striking: “Humans are increasingly detached from decision-making spatially as well as temporally and in terms of rational distancing and cognitive displacement.” When human and algorithmic intelligence became unbalanced, three effects emerged: “deferred decisions, workarounds, and (data) manipulations.” Users who did not trust algorithmic decisions would avoid making certain choices or create false feedback to circumvent the system.
The implications for design are profound. Algorithmic recommendation systems do not merely surface content; they shape the conditions under which creative decisions are made. As Chayka documented in Filterworld, the rule of algorithmic culture is convergence. Content that deviates from established patterns receives less amplification. Creators learn, consciously or unconsciously, to produce work that fits the template. The result is not censorship in any traditional sense but a soft infrastructure of conformity, enforced through engagement metrics, visibility algorithms, and economic incentives.
This dynamic is particularly visible in user interface design, where the shift from editorial and community-driven decisions to algorithmic ones has been documented by scholars studying recommender systems. As one study in the journal Information, Communication & Society noted, this involves “a shift from traditional media institutions that sought to uphold and balance public-oriented values like equality, diversity or accountability in editorial decisions.” With recommender systems, “decisions about algorithmic rules are made far from the publics they affect, with limited transparency or mechanisms for democratic oversight or control.”
Research from Springer's AI & Society journal has further explored the challenges of enabling user control over algorithm-based services. The opacity of algorithmic systems means it is not clear how much they truly serve their users. Giving users genuine control demands what researchers call “algorithmic literacy”: the ability to interrogate one's own dispositions and formalise them in ways that can be translated into the algorithmic system. This is a high cognitive bar that most users cannot clear, which means that in practice, the algorithm's defaults prevail. And those defaults, in design contexts, skew overwhelmingly toward minimalist uniformity.
The minimalist interface itself serves a strategic function within this system. Shoshana Zuboff, the Harvard Business School professor emerita who coined the term “surveillance capitalism,” has documented how technology companies implement what she calls a “hiding strategy”: clean, simple interfaces that conceal the vast apparatus of data extraction operating beneath the surface. “Surveillance capitalism unilaterally claims human experience as free raw material for translation into behavioural data,” Zuboff wrote in The Age of Surveillance Capitalism (PublicAffairs, 2019). The minimalist interface is not merely an aesthetic choice; it is a mechanism for rendering the machinery of surveillance invisible. The simpler the surface, the more effectively it conceals the complexity, and the power, operating beneath it. Google's search page remains perhaps the most famous example: a near-empty white field that conceals one of the most sophisticated advertising and data-extraction infrastructures ever built.
Who Gains from Defining the Essential
The question at the heart of minimalism's transformation from philosophy to default is ultimately one of authority. When every surface is stripped to “essential” elements, who holds the power to define what counts as essential? The answer, in practice, is a remarkably concentrated group: platform operators, branding consultancies, venture capital investors, and the technology companies whose products set the template for global design norms.
This concentration of aesthetic authority has measurable consequences. When Nadine Chahine warns that brands homogenised into a similar look means “we're losing something as designers and as a community,” she is describing a loss of collective agency over visual culture. When Astrid Stavro argues that stripping brands of unique elements means “stripping them of their soul and heart,” she is describing a loss of meaning that no amount of user testing can recapture. When Celine Semaan traces minimalist standardisation back to colonial routes of extraction, she is describing a power structure that long predates the internet but has been amplified by it.
The losses are not evenly distributed. Wealthy consumers can afford bespoke design that expresses individual identity. They can hire architects who work outside the minimalist template, commission custom furniture, and curate interiors that reflect personal histories and cultural affiliations. The minimalist default falls most heavily on those who cannot opt out: renters in algorithmically optimised Airbnb properties, users navigating interfaces designed to maximise data extraction rather than cultural expression, communities whose vernacular design traditions are displaced by the “universal language” of international minimalism.
There is a class dimension here that deserves direct attention. Minimalism, as a lifestyle aesthetic, presupposes the ability to choose less. It is a luxury of those who have enough. The person who owns three carefully selected items of clothing in neutral tones is performing a different social act from the person who owns three items of clothing because that is what they can afford. The visual language is identical; the power relations are opposite. When minimalism becomes the unexamined default of consumer culture, this distinction collapses, and an aesthetic born of privilege masquerades as universal good taste.
In May 2024, the World Intellectual Property Organization adopted a treaty requiring patent and design applicants to disclose where traditional knowledge or genetic resources originate, the first time a WIPO treaty has named Indigenous Peoples directly. This legislative recognition of design's power dynamics suggests a growing awareness that the authority to define “essential” is not a neutral act of aesthetic judgement but an exercise of power with material consequences.
Reclaiming Complexity
The backlash against minimalist homogenisation is not merely aesthetic nostalgia. It represents a political demand for distributed authority over the visual environment. Indigenous designers are at the forefront of this reclamation. At Native Fashion Week in Santa Fe, designers have incorporated traditional motifs into contemporary collections as a way to reclaim cultures that were appropriated by non-Native designers. In Winnipeg, architect Reanna McKay is working on projects like the Wehwehneh Bahgahkinahgohn, where Indigenous heritage and the connection to nature are represented in the architecture itself, encompassing residential, assisted living, museum, ceremony, and educational spaces.
In South Africa, 2025 interior design trends are embracing cultural specificity over homogeneity, with Nongo baskets being reimagined as art and designers leveraging indigenous crafts to create heritage-driven spaces. In Canada, design education programmes are teaching students about how settler-colonial practices disconnected Indigenous peoples from their roots, traditions, and ceremonies, and how design can serve as a vehicle for reconnection rather than erasure.
The branding world, too, shows signs of fracture in the minimalist consensus. Burberry's return to its heritage logo in 2023 was not an isolated case. Vivienne Westwood, the iconic British designer, refused to follow the sans-serif trend entirely, maintaining her punk-inflected identity whilst other fashion houses capitulated. Avon modernised its logo without abandoning character, discarding the minimalistic sans-serif typeface and adopting a design reminiscent of its 1970s identity. Sarah Hyndman, a typographer and researcher, told D&AD that when she asked a friend's 15-year-old daughter whether she found current fashion logos aspirational, the response was: “No, they're too blocky and bland.” But heritage logos? “Yeah we love nostalgia.”
These are not marginal developments. They represent a fundamental challenge to the assumption that minimalism's “universal legibility” is either universal or legible. Tunstall's Decolonizing Design offers practical frameworks for institutional transformation. Watson's Lo-TEK documents technologies that have sustained communities for thousands of years. Semaan's advocacy connects contemporary design practice to ongoing structures of extraction and control. The question is not whether minimalism will persist; it will, because it serves genuine functions. The question is whether minimalism will continue to operate as an unexamined default, a background assumption so pervasive that deviation from it requires justification, or whether it will be recognised for what it has become: one aesthetic option among many, with its own politics, its own exclusions, and its own beneficiaries.
When every surface is stripped to essentials determined by designers and algorithms rather than communities and users, the loss is not merely decorative. It is a loss of the authority to define one's own visual environment, to embed meaning in surfaces, to express cultural specificity in the spaces where life is lived. The clutter that minimalism promised to clear away was never just clutter. It was complexity, history, identity, and difference. And the clean white space that replaced it is never as neutral as it appears.
References & Sources
- Kyle Chayka, “Welcome to AirSpace,” The Verge, 2016. https://www.theverge.com/2016/8/3/12325104/airspace-aesthetic-software-gentrification-startup-office
- Kyle Chayka, Filterworld: How Algorithms Flattened Culture, Doubleday, 2024. https://www.kylechayka.com/filterworld
- Radek Sienkiewicz, “Why do so many brands change their logos and look like everyone else?” VelvetShark. https://velvetshark.com/why-do-brands-change-their-logos-and-look-like-everyone-else
- Nadine Chahine, Astrid Stavro and Sarah Hyndman, quoted in “Beyond the sans serif: how type can move on from 'blanding,'” D&AD. https://www.dandad.org/insights/features/beyond-sans-serif-how-type-can-move-blanding-awards-insights
- Celine Semaan, “We must confront design's colonial inheritance,” Dezeen, August 2025. https://www.dezeen.com/2025/08/07/colonial-design-celine-semaan-opinion/
- Elizabeth (Dori) Tunstall, Decolonizing Design: A Cultural Justice Guidebook, MIT Press, 2023. https://mitpress.mit.edu/9780262047692/decolonizing-design/
- Julia Watson, Lo-TEK: Design by Radical Indigenism, Taschen, 2019. https://www.juliawatson.com/lo-tek-design-by-radical-indigenism
- Shoshana Zuboff, The Age of Surveillance Capitalism, PublicAffairs, 2019. https://www.hachettebookgroup.com/titles/shoshana-zuboff/the-age-of-surveillance-capitalism/9781610395694/
- Verena Bader and Stephan Kaiser, “Algorithmic decision-making? The user interface and its role for human involvement in decisions supported by artificial intelligence,” Organization, 2019. https://journals.sagepub.com/doi/10.1177/1350508419855714
- “Is the DTC brand aesthetic bad for business?” Retail Dive, 2021. https://www.retaildive.com/news/is-the-dtc-brand-aesthetic-bad-for-business/588062/
- “Opinion: The brands and playbook that defined the DTC decade,” Glossy. https://www.glossy.co/fashion/opinion-the-brands-and-playbook-that-defined-the-dtc-decade/
- “DTCs are facing a copycat problem,” Modern Retail. https://www.modernretail.co/retailers/dtcs-are-facing-a-copycat-problem/
- “Meet the Surprisingly Small Group of Branding Shops Behind Today's Top Challenger Brands,” Adweek. https://www.adweek.com/brand-marketing/meet-the-surprisingly-small-group-of-branding-shops-behind-todays-top-challenger-brands/
- Boult, “'Blanding' of iconic logos.” https://www.boult.com/bulletin/blanding-the-loss-of-value-in-fashion-logos/
- “AirSpace: The Decline of Airbnb Aesthetic in 2024,” nss magazine. https://www.nssmag.com/en/lifestyle/41707/airspace-aesthetic-decline-airbnb-2024
- “Inequality By Design? Why we need to start talking about aesthetics, design and politics,” LSE Sociology Blog, 2016. https://blogs.lse.ac.uk/researchingsociology/2016/09/12/inequality-by-design-why-we-need-to-start-talking-about-aesthetics-design-and-politics/
- “Cultural Homogenization and the Decline of Vernacular Architecture,” International Journal for Multidisciplinary Research, 2025. https://www.ijfmr.com/papers/2025/2/39067.pdf
- Matt Johnson, Professor of Psychology and Marketing, Hult International Business School. Author of Branding That Means Business, Economist Books, 2022. https://www.neuroscienceof.com/
- Minimalist Lifestyle Products Market report, FutureDataStats, 2024. https://www.futuredatastats.com/minimalist-lifestyle-products-market
- “Individual choice, collective effects: recommender systems, law by design, and the DSA's double choice architecture,” Information, Communication & Society, 2025. https://www.tandfonline.com/doi/full/10.1080/1369118X.2025.2595663
- “Challenges in enabling user control over algorithm-based services,” AI & Society, Springer. https://link.springer.com/article/10.1007/s00146-022-01395-1
- Peter Saville, quoted in “Burberry logo redesign 'totally and utterly irresponsible' says Peter Saville,” Dezeen, June 2025. https://www.dezeen.com/2025/06/13/burberry-logo-redesign-irresponsible-peter-saville/
- “Burberry unveils 'archive-inspired' charging knight logo,” Dezeen, February 2023. https://www.dezeen.com/2023/02/07/burberry-daniel-lee-logo-equestrian-knight-design/
- “Is Silicon Valley's Love Affair With Direct-to-Consumer Brands Over?” Business of Fashion. https://www.businessoffashion.com/articles/entrepreneurship/venture-capital-vc-direct-to-consumer-dtc/
- Laurel Schwulst, quoted in “How 'International Airbnb Style' Became the Dominant Aesthetic of Our Time,” Longreads, 2017. https://longreads.com/2017/05/18/airbnb-design-aesthetic/

Tim Green UK-based Systems Theorist & Independent Technology Writer
Tim explores the intersections of artificial intelligence, decentralised cognition, and posthuman ethics. His work, published at smarterarticles.co.uk, challenges dominant narratives of technological progress while proposing interdisciplinary frameworks for collective intelligence and digital stewardship.
His writing has been featured on Ground News and shared by independent researchers across both academic and technological communities.
ORCID: 0009-0002-0156-9795 Email: tim@smarterarticles.co.uk
Listen to the free weekly SmarterArticles Podcast
from  💚
💚

A double-standard to fury Portuguese alone with smile Citizens in days of a million This kurt and social will And he’s the liar and not the last A praying Jin Wanted out And these two inner dance For policy a blip and first Can’t stand for peace- in that man’s car,- a feeling And the column line of her A misery in that A total cancer on anyone then,- Spaces of they are And all this pomp Shall Earth allow this stuff- to happen to them And again we’ll sign the lease Men will erupt to democracy And Holland sees a way The future for this ambulance And called a country- finding hell Judging at the rodeo And the moment one is other And in an instant, double-earthquake This evening is unwell Flags on hand to show support For sins regret to keep And coal alive to each his gen The mystery is not lost For days and that The line of web With tort of jaw And distance to the tow And make this loud There will be peace in Alberta And on the day of purpose to us all Sitting eyes to wonder Is it them or news and distant shore The policy of truth Captain Wise and whereabouts Silencing Rome at rite And to this pay of Texas Fortune replied to him That this and that is they And where it isn’t reune- We’ll fight for reality And justice to our year And nights renew For this fortune in our time Close to Darwin and resist The time of burden is our oar And lazy cover Then of day The truth in them to see Rapture us all, our King in Heaven And they have war with the Saudis So whereabout in war The shock of this whole country Watching photos to the door Of raiding space to visit They unto and sit with mercy Because of tort remain And the other and the two are same Burning by the altar Never then to be Men of true rapport To those at peace and willing Story, love, peace- is not them And saints to say so- who wonder at our goal- and where we are- in China.
Before the Water Turned Silver
from Douglas Vandergraph
Chapter One
Jesus stood alone at the far end of the breakwater where the concrete gave way to wet stone and barnacled posts. The town behind Him was still dim, its harbor lamps thinning against the first hint of morning, and the gulls had not yet started their full loud argument over the docks. He had come before daylight, as He often did, to pray where the wind could touch His face and the whole sleeping town seemed to breathe in one slow body. He prayed for the women who would open the cafés before sunrise and for the men who would come in smelling like diesel and salt. He prayed for marriages living under strain, for children learning how to hide hurt, for those who feared the truth because they were sure it would cost more than they could survive. When He lifted His eyes at last, He looked not toward the open water first, but toward Slip Nine, where a charter boat was easing in too fast for the hour.
Noah Mercer cut the engine hard and let the boat thump the fenders. He had spent the whole night out where the water darkened and flattened and gave him too much room to think. The cooler held three snapper, which was almost insulting after nine hours on the water, and his phone held six missed calls from his mother and one text he had read twice without answering. She had written that she was coming by the dock this morning whether he wanted company or not. Under that message, still open in the browser he had not meant to leave running, was a video he had clicked and never finished: Jesus restores Peter after failure by the sea. Below it sat a tab from a late-night reading spiral, an old reflection he had saved because the title bothered him in a way he could not explain: the mercy waiting on the shoreline.
He shoved the phone into his jacket and climbed out without looking toward the parking lot. His shoulders hurt from hauling wet line, but that was not what made him move like a man older than thirty-eight. The real heaviness sat lower and quieter. It had been there for eleven months, ever since the last voicemail his younger brother left from outside the county detox center. Noah had heard the message, heard the shaking in Caleb’s voice, and still put the phone facedown on the table because he was tired of being frightened and tired of being used and tired of being the one who always came. Caleb died before sunrise in the alley behind a liquor store three blocks from the building where he had been released. Their mother still thought Noah never got the call.
The dock boards were slick with old spray. Noah bent to rope off the stern, then stood with the line in his hand longer than he needed to, staring into the black water between the pilings. The harbor had its own smell before dawn, a mix of salt, bait, gasoline, and the sweet rot of old wood. Most mornings he could tolerate it. Some mornings it felt like standing inside a memory he could not scrub out. Caleb used to love this hour. He used to say the water told the truth before people got up and started lying about themselves. Noah had laughed when he was twenty and Caleb was nineteen and both of them still believed there would always be time to make things right later.
A cart rattled across the lot behind him. He turned too quickly, thinking for a moment it might be his mother’s old station wagon, but it was only Mrs. Alvarez from the café carrying milk crates inside. She raised a hand, and he managed the sort of nod that passed for politeness when a man had not slept. The café windows were still dark, though one yellow light had come on in the kitchen. In half an hour the regulars would gather there, harbor men with stiff hands and weather maps folded into their pockets, and he would have to decide whether to sit among them and pretend the day was ordinary.
He heard footsteps on the dock, not hurried, not cautious either. Just steady. He did not turn right away. People who wanted something from him usually announced themselves with a kind of impatience before they even spoke. These steps did not have that sound.
“You ran too far south,” a man said.
Noah looked over. He saw a stranger wearing a dark coat that had taken the mist without seeming damp, and work boots that looked as though they belonged on the same dock as everyone else’s and yet somehow did not. He was not old, though there was something settled in His face that made age feel like the wrong measurement. His hair moved in the wind. His hands were empty. He stood as if there were no reason in the world to rush the next thing He was going to say.
Noah gave a short humorless breath. “That so?”
“The current turned on you before midnight.” The man glanced toward the horizon, where a thin silver line had started to gather under the clouds. “You kept going because you did not want to come back empty.”
Noah almost asked who had been watching him, but the words felt childish before he formed them. “If you know so much about fishing, you could’ve come along.”
The man smiled, though not like someone who had been insulted. “You would not have invited Me.”
That should have ended the exchange. Noah had no appetite for strangers before coffee, especially strangers who sounded like they had been reading his thoughts. He started toward the dock box, but the man moved with him, not crowding, only keeping pace.
“There’s coffee in the café in ten minutes,” Noah said. “If you’re waiting for someone, wait there.”
“I am waiting for someone.”
Noah looked at Him again, more directly this time, and something inside him tightened. The man’s face held no trace of mockery, no salesman’s eagerness, no churchman’s polished concern. What unsettled Noah was the lack of performance. He had spent almost a year avoiding any room where people might try to help him feel better. He had learned how quickly pity could turn theatrical. This man seemed free of it, as if He could stand beside someone’s hurt without needing to decorate it or shrink from it.
Mrs. Alvarez opened the back café door and propped it with a flour sack. Warm light spread in a pale wedge across the dock. The smell of onions hitting butter drifted out, followed by coffee, and something in Noah’s chest clenched so fast it made him angry. Caleb used to come in off the boats and order eggs no matter the time of day. He had said breakfast was the only meal honest enough for the morning because it did not pretend the day had already gone well.
Noah yanked open the dock box and began coiling line that did not need coiling. “You from around here?”
“I am where I am needed.”
He said it simply, with no weight added for effect. Noah hated that the answer should have sounded ridiculous and somehow did not.
“You with one of those mission groups?” Noah asked. “Church outreach, grief counseling, that kind of thing?”
“No.”
Noah shut the lid harder than necessary. “Then what do you want?”
The man was quiet for a moment. The gulls had begun waking now, one cry after another, and from town came the low groan of a delivery truck backing into the market lane. The harbor was slowly becoming itself again, all labor and movement and things that needed doing. Still, around the two of them, the morning seemed held.
“I want you to stop punishing yourself in secret while pretending you are protecting everyone else,” He said.
Noah went still.
It was not only the words. It was the calm with which they were spoken, as if the man had just named the weather. Noah felt the first hard pulse of fear under his ribs, the kind that had nothing to do with physical danger and everything to do with being known.
He laughed once, but there was no humor in it. “You don’t know anything about me.”
The man did not answer immediately. He looked past Noah toward the cabin of the charter boat, where a faded blue duffel sat on the bench inside the window. Caleb’s duffel. Noah had meant to take it home months ago, but the bag had remained there like a sentence he could not finish reading.
“You heard your brother’s voice,” the man said. “You knew he was alone. You let the night keep moving because you could not bear one more rescue that might fail.”
Noah took one step back. The dock rocked under him though the tide was not strong enough to justify it. Every instinct he had rose at once, not toward confession but toward anger, because anger was the fastest wall he knew how to build.
“Who told you that?” he said, and his voice came out low and ragged. “My mother? Was it Pastor Glenn? Because if they sent you down here—”
“No one sent Me.”
The answer should have been impossible. Noah knew that. He knew there were only three people in the world who had known about the voicemail, and one of them was dead. Yet the man stood there without triumph, without pressure, not exposing Noah for the pleasure of having found him out. He looked grieved, if anything, though not with surprise. More like someone who had been standing near a locked room for a long time, waiting for the person inside to stop leaning against the door.
Mrs. Alvarez stepped onto the dock with a chalkboard sign under her arm. She looked from Noah to the stranger and smiled the easy smile of a woman who had worked too many mornings to be afraid of silence in men.
“Coffee’s on,” she said. “You two can freeze out here or come inside like sensible people.”
The man inclined His head to her in thanks. Noah could not speak.
Mrs. Alvarez went back in, humming under her breath. The sound made the dock feel almost unbearably normal.
The man turned toward the café door, then paused as if giving Noah room to refuse. “Come eat,” He said. “You have been hungry longer than you think.”
It was a strange thing to say to a man who had spent the whole night with a sandwich sweating in wax paper beside the wheel. But Noah knew at once He was not talking about that. He also knew that if he followed this stranger into the café, the day would become something other than what he had prepared himself to survive.
Across the parking lot, his mother’s station wagon turned slowly in at the harbor entrance, its left headlight still clouded from the accident she never fixed. Noah felt the old instinct rise in him, the one that had governed nearly a year of his life. Keep it together. Say as little as possible. Get through the morning. Protect her from the truth. Protect yourself from what the truth will cost.
The man waited beside the open café door, one hand resting lightly against the frame. Warmth and coffee and the low clatter of plates came from inside. Beyond the lot, his mother parked and sat for a moment with both hands on the steering wheel, as if gathering herself before stepping out into another day of not knowing.
Noah stood between the boat and the door and the car, with the salt wind on his face and the taste of old fear rising in his mouth. For the first time in months, he did not feel cornered by memory alone. He felt seen inside it.
Then the man spoke again, quietly enough that Noah had to lean inward to hear Him over the gulls.
“The truth will wound what the lie has already been starving,” He said. “But it will not destroy what love has been keeping alive.”
Noah did not move for several seconds. Then, before he could talk himself back into the smaller version of the day, he followed the stranger into the light.
Chapter Two
The café had only six tables, a counter with cracked red stools, and windows clouded at the edges by years of salt air. Noah had been inside it a hundred times, maybe a thousand, but that morning every familiar object seemed sharpened by the fact that he was walking in beside a man he could not explain. Mrs. Alvarez looked up from the griddle, took them in with the quick practical glance of someone who had raised children and buried a husband and no longer believed every silence needed filling, then pointed them toward the back booth near the window. A radio low on the shelf behind the counter muttered weather and headlines to no one in particular. Steam rose from a pot of chowder she was starting for lunch, and coffee darkened the room with its burnt, comforting smell.
Noah slid into the booth because standing felt more dangerous. The stranger sat across from him, not like a guest waiting to be served, but like someone fully at ease in a place where tired people came to be fed. The vinyl seat sighed under His weight. Mrs. Alvarez brought two mugs without asking what they wanted.
“You look terrible,” she said to Noah, setting his down first. “And if you say you’re fine, I’m charging you extra.”
Noah almost smiled in spite of himself. “That’s robbery.”
“That’s discernment.” She turned toward the man across from him. “You new in town?”
“For now,” He said.
She studied His face for half a second, and some private recognition seemed to move through her features, not the recognition of memory exactly, more the kind that comes when something quiet in a person settles. “Then for now you’re getting eggs whether you asked for them or not. He doesn’t eat enough when he’s had a bad night.”
She went back to the counter. Noah kept his hands around the mug, though the coffee was too hot to drink. Outside the window his mother’s station wagon remained in the lot. He could see her now through the streaked glass, sitting in the driver’s seat with her head bent. He knew that posture. She was praying. She had done that for years before stepping into hard rooms, sometimes with real peace afterward, sometimes only with enough strength to keep from collapsing in front of other people.
“She prays before she sees you,” the man said.
Noah looked up sharply. “Everybody prays before they see me now?”
“She has been asking for courage, not information.”
Noah stared at the black surface of his coffee. “Same thing, usually.”
“No.” The man’s voice was gentle, but it carried that settled weight again, the kind that made ordinary words open wider than they should. “Information can arrive before a soul is ready to bear it. Courage is what helps a soul receive what is true and remain standing.”
Noah wanted to answer with something sharp, something that would pull the conversation back down to a size he could control, but he did not trust his mouth. Mrs. Alvarez slid two plates onto the table with the efficiency of a woman who understood that feeding people was sometimes more merciful than questioning them. The eggs were soft and bright, the toast thick, the potatoes crisped with onion and pepper. Noah realized he was hungrier than he had let himself feel.
The man bowed His head for a brief moment before touching the food. It was not showy and it was not hurried. Noah had seen enough prayers over meals to know the difference between habit and presence. This felt like neither. It felt as though the quiet around the table had been listened into.
Noah took one bite, then another, and hated the sudden sting behind his eyes. The food was simple. That was what made it worse. Grief had a way of making ordinary kindness unbearable because it reminded the body it still wanted to live.
His mother finally opened the car door and stepped out. She wore the green coat she had owned since Noah was in high school, though the hem had frayed and one button had been replaced by a darker one that did not quite match. Her hair, once the same dark brown Caleb’s had been, had gone mostly silver in the past year. She moved more carefully now, as if every surface might shift under her weight. Noah watched her pause in the lot and look toward the harbor before coming to the café door.
“You can still leave,” he said.
“I know,” the man answered.
“That isn’t what I meant.”
“I know that too.”
The bell over the door gave a tired metallic ring. His mother came in carrying a paper sack folded tight at the top. Her eyes found Noah first, then the man across from him, then the untouched half of Noah’s toast. Relief and caution crossed her face so quickly they almost looked like the same expression.
“There you are,” she said. “I called.”
“I know.”
“You didn’t answer.”
“I know.”
She stood at the table a moment longer, searching him with the old mother’s habit that could still make him feel fourteen and guilty before she had any evidence. Mrs. Alvarez called out from the counter that there was fresh coffee if she wanted it. His mother thanked her, set the paper sack on the bench beside Noah, and looked at the stranger.
“I hope I’m not interrupting.”
“No, ma’am,” He said. “Please sit.”
There was nothing strange in the sentence itself, but the way He said it made the invitation sound as though it had carried her name long before she entered the room. She slid into the booth beside Noah and laid her gloves in her lap. Her hands were trembling lightly, not enough that anyone else would notice. Noah noticed because he knew the rhythms of her body the way children do, even when they have become grown men with too much distance between them.
Mrs. Alvarez brought a mug and poured without asking. “He looks worse than last week,” she said softly to Noah’s mother.
“That’s because he sleeps with engines and bad decisions.” She tried for lightness, but it thinned before the sentence finished. Her eyes went back to Noah. “Did you sell enough to cover fuel?”
“Almost.”
“Almost isn’t yes.”
“It’s close enough for a Tuesday.”
She nodded as though accepting the answer, though her mouth tightened. Then she tapped the paper sack with two fingers. “I found this while I was cleaning the hall closet. It’s Caleb’s watch. I thought maybe you’d want it if you’re still keeping his other things on the boat.”
Noah felt the booth narrow around him. “You went through the closet?”
“I live there too, Noah.”
“That’s not what I asked.”
She held his gaze for a second, then looked down. “I’m tired of opening doors and finding him nowhere. I thought maybe if I put some things in one place I could breathe in that house again.”
The man across from them ate quietly, as if giving the words room to be themselves. Noah wished He would speak and resented the wish the moment he felt it. He was used to being the one who managed silence. He was not used to silence exposing the edges of what he was hiding.
His mother wrapped both hands around her mug. “I also found some paperwork from the detox center,” she said. “Release forms. They were in his coat pocket for some reason. I don’t know why he brought them home.”
Noah set down his fork.
“He signed out?” he asked, though he already knew. He heard how flat the question sounded and hated that too.
“They released him in the evening.” She watched him carefully now. “I never knew what time. I don’t know why that matters to me, but it does.”
The man lifted His eyes and looked at Noah, not pressing, only present. Noah felt the blood in his face. He could see the voicemail in his mind again, the glowing screen, Caleb’s voice thick with fear and exhaustion, the way he had said Noah’s name first with forced cheer, then again with less of it, then finally with no disguise at all.
His mother kept speaking, almost as if the movement of her own words was the only thing keeping her steady. “I’ve gone over that night so many times. I know it doesn’t change what happened. I know people die at all hours, with or without our understanding. But there are pieces I can’t stop touching in my mind, and one of them is whether he tried to reach anyone after they let him go.”
Noah’s hand tightened around the fork until the metal hurt.
Mrs. Alvarez called an order to the kitchen window though there was no one back there but herself. Outside, a truck rattled over a pothole. Somewhere at the counter a man laughed at something on the radio. The ordinary world continued without asking permission from grief, and that had always felt to Noah like one of the cruelest facts of being alive.
His mother waited. Then, as if trying to soften the question before it landed, she added, “You would tell me if you knew something, wouldn’t you?”
He heard the lie forming before he made it, the old well-worn instinct already reaching for him. He could protect her one more day. He could say no. He could keep the secret where it had lived so long it almost felt structural, like a beam inside the house of his life that everything else leaned on.
“I don’t know anything more than you do,” he said.
The sentence entered the booth and sat there like smoke. His mother nodded too quickly, which was its own kind of hurt, the kind that says a person has accepted less than hope because asking for more feels dangerous. She took a sip of coffee she did not want.
The man set down His fork and folded His hands. He did not look at Noah first. He looked at Noah’s mother.
“Grief makes people lonely in different rooms,” He said. “Sometimes they think silence is a way of loving each other. Usually it is only a way of starving together.”
Noah’s mother blinked, startled not by offense but by recognition. “That sounds true,” she said quietly.
Noah felt anger leap up, clean and fast because the sentence had gone straight through him. “You don’t get to come in here and turn breakfast into counseling.”
The man turned toward him then, and there was no defensiveness in His face, no sign that He had been wounded by the outburst. What Noah saw instead was sorrow so steady it made his own anger feel small and frantic.
“I did not come to shame you,” He said. “You have done enough of that to yourself.”
Noah pushed back from the booth so suddenly it scraped the floor. Mrs. Alvarez looked over from the counter. Noah muttered that he needed air and walked out before either of them could answer. The bell over the café door snapped once against the glass.
The harbor wind hit him hard enough to make his eyes water. He went past the bait freezer, past the stack of lobster pots no one had collected yet, and stopped at the end of the dock where the water slapped the pilings in a quick broken rhythm. Boats moved in and out of the slips farther down, morning charters already loading coolers and talking too loud. He could feel the phone in his jacket pocket like a hot stone.
The café door opened behind him. He assumed it would be his mother and braced for it, but it was the man. He came to stand a short distance away, near enough to speak without raising His voice, far enough that Noah did not feel trapped.
“She deserves better than this,” Noah said before the man could speak.
“Yes.”
The answer startled him. He had expected comfort, or at least a gentler phrasing. Instead it came cleanly, without cruelty and without softening.
Noah stared out at the water. “I know that.”
“Yes.”
“And if I tell her now, after all this time, what is that? Mercy? Honesty? It sounds more like another cruelty I waited a year to deliver.”
“It will be pain,” the man said. “But pain is not always cruelty. Sometimes it is the first honest thing to enter a room in a very long time.”
Noah laughed once, bitterly. “You make it sound simple.”
“I did not say it was simple.”
The gulls had grown louder. Sunlight was reaching into the harbor now, laying pale strips across the water so that every ripple caught and released the light before it could settle. Noah put both hands on the rail and lowered his head.
“I heard him,” he said. The words came out rough. “He called from outside the center. He said he needed a ride. He said he didn’t trust himself walking. I let it ring. Then I listened later and did nothing.” He swallowed hard. “You tell me what kind of brother does that.”
The man did not answer at once. When He did, His voice was low enough that the wind nearly took it.
“A frightened one. A weary one. A man who had mistaken the end of his strength for the end of his love.”
Noah shut his eyes. The sentence hurt because it did not excuse him and yet somehow refused to reduce him to one night.
“He still died alone.”
“Yes.”
That word again, with no attempt to negotiate it into something easier. Noah had never hated and needed truth so much at the same time.
Behind them the café door opened once more. His mother stood there in the doorway holding Caleb’s watch in one hand, not interrupting, only watching. Noah did not know how much she had heard. Perhaps enough. Perhaps everything that mattered.
The man beside him spoke without turning.
“You cannot confess in fragments forever,” He said. “Soon you will have to decide whether the truth belongs only to your punishment or also to her healing.”
Noah lifted his head. His mother’s face had gone colorless, but she had not collapsed. She had not screamed. She stood in the morning light looking smaller than he had ever seen her and yet not weak, only pierced.
For one suspended moment the whole harbor seemed to wait with him: the gulls circling above the slips, the engines idling, the lines pulling against cleats, the smell of salt and coffee and fuel. Noah looked from his mother to the man beside him, and the thing that terrified him most was no longer that the truth would destroy what remained. It was that love had been standing near it all along, asking to be trusted.
Chapter Three
His mother did not come down the dock right away. She stood in the café doorway with Caleb’s watch curled into her palm, as if any sudden movement might break whatever fragile thing had finally come into the light. Noah knew that look on her face. He had seen it in hospital rooms and in the chapel at the funeral home and once, years before, when Caleb was sixteen and had disappeared for two days with men neither of them trusted. It was the look of someone whose heart had already survived a great deal and understood, before the mind did, when another blow was coming.
She crossed the dock slowly, the hem of her coat lifting in the wind. When she reached them, she stopped a few feet away and looked first at Noah, then at the man beside him. Her eyes held neither accusation nor softness yet. They held the kind of attention pain gives when it no longer has the strength for performance.
“Did he call you?” she asked.
Noah opened his mouth and felt how useless words could be when they had been delayed too long. The first instinct in him was still to answer with less than the whole truth, to trim the edges, to say just enough that the moment could pass without complete collapse. But the lie had gone rotten inside him. He could feel it now, not as protection but as decay.
“Yes,” he said.
The word entered the morning cleanly. His mother closed her eyes for a brief moment, then opened them again.
“The night he died?”
“Yes.”
She looked away toward the water, and Noah could almost see her counting through the waves of it, not to calm herself exactly, but to remain upright inside what she had heard. When she spoke again, her voice was quieter.
“What time?”
“A little after ten.”
The gulls circled above the slips. Somewhere across the harbor a man called for more ice. The ordinary day kept moving, and Noah wanted to hate it all over again, the injustice of how human grief had to happen in the same world where engines started and doors opened and people joked over coffee. Yet standing there with his mother’s face turned away from him, he realized he had been using the noise of normal life as a hiding place. As long as there had been work to do, fuel to buy, nets to mend, bills to curse, he had been able to pretend the worst thing in him was still waiting for a proper moment to be dealt with.
His mother opened her hand and looked down at Caleb’s watch before closing her fingers around it again. “Did he ask you to come get him?”
Noah felt his throat tighten until it hurt. “Yes.”
She nodded once, but did not look up. “And you didn’t go.”
It was not a question. The terrible mercy of that was that it left no room for strategy. Noah could not shape the scene into something less final. He could only stand in it.
“No,” he said. “I didn’t go.”
This time his mother did look at him. He expected anger first. He expected the shock of betrayal, or the old hard line she used to get around her mouth when Caleb had stolen money and promised, one more time, that he would make it right. Instead he saw something sadder and harder to bear. She looked like a woman trying to understand where to place a new weight inside a heart already carrying too much.
“Why?” she asked.
Noah pressed his hands against the cold rail until the metal bit his skin. He had imagined this question in one form or another for months, usually late at night when the harbor was quiet and sleep kept its distance. In those private rehearsals he had gathered phrases that sounded almost reasonable. I was exhausted. I thought he was manipulating me again. I had already paid for treatment twice. I didn’t know it was that bad. But here, under his mother’s eyes, with the strange steady man beside him and the morning widening all around them, those phrases felt like polished stones over a grave. True in pieces, perhaps, but arranged to keep anyone from seeing the depth.
“Because I was angry,” he said at last. “Because I was tired of being afraid every time the phone rang. Because I thought if I went that night, there would only be another night after that and another after that, and I couldn’t keep doing it.” He swallowed hard. “And because some ugly part of me wanted him to feel the consequence of being alone for once.”
His mother flinched, though he could not tell whether it was the confession itself or the fact that he had spoken it aloud. Noah wished he could take the words back and also knew that for once there was no mercy in taking anything back.
The man beside him had not moved. He stood with the wind touching the front of His coat and His eyes on Noah’s mother now, not intruding, not withdrawing. Noah had the strange sense that He was honoring her grief by refusing to rush its first shape.
She looked out at the water again. “I kept my phone on silent that week,” she said, almost to herself.
Noah turned toward her. “What?”
She gave a small brittle laugh that broke halfway through. “You weren’t the only one who was tired.” She rubbed her thumb over the crown of Caleb’s watch as if trying to polish away years from its scratched face. “Every vibration made my chest hurt. Every unknown number felt like some new damage arriving in my hand. I told myself that if he truly needed me, he would call twice, or you would call, or someone else would find me. I slept with the phone silenced in the kitchen drawer.” She looked up at Noah then, and tears had finally gathered in her eyes, though they had not yet fallen. “I didn’t know he called you. But I have spent months wondering whether he called me too and whether I simply arranged my own peace so I wouldn’t have to hear him.”
The confession landed between them with a gentleness that made it no less devastating. Noah had carried his guilt like a private chamber with the door bolted from the inside. Hearing his mother speak, he understood for the first time that she had been kneeling outside a different locked room all along, certain that her own hidden failure would crush him if she named it. He had thought silence was the shape of his punishment. He had not seen how it had become the shape of their separation.
The man turned His face toward the water, giving them the dignity of not being watched too closely. Noah’s mother stepped nearer the rail, her shoulder now almost level with Noah’s.
“I need you to understand something,” she said. “I am hurt. I am more hurt than I know how to say yet. But I am not hurt because you were the only one who failed him. I am hurt because you have been standing in this alone while sitting ten feet from me in my own kitchen.” Her voice wavered, but it did not break. “Do you know what it is like to lose one son and then slowly realize the other one has been disappearing into shame right in front of you?”
Noah lowered his head. He could not remember the last time someone’s pain had entered him without first turning him defensive. This time there was no room for defense, only a sorrow so clear it felt almost like clean water.
“I thought if you knew,” he said, “you’d never look at me the same way again.”
His mother drew a long breath. “That was already true.” When he looked at her, startled, her face softened. “Not because I knew this. Because grief changes a mother’s eyes whether she wants it to or not. I haven’t looked at anyone the same way since Caleb died. But that doesn’t mean I stopped loving you. It means I’ve been trying to find you in the dark and didn’t know where you’d gone.”
The wind shifted, carrying the smell of coffee and hot oil from the café, along with the deeper salt smell of the harbor itself. Sunlight had strengthened now, turning the surface of the water from iron to silver in long broken ribbons. Boats farther out moved through that brightness like small dark thoughts.
Noah looked at the man beside them. “What am I supposed to do with this now?” he asked, and his voice sounded smaller than he had intended, almost like the voice of a boy standing in the ruins of something he had broken with his own hands.
The man turned back toward him. There was no distance in His face. There was grief there, and something stronger than grief, something Noah did not yet know how to name without sounding foolish.
“You tell the whole truth,” He said. “You stop using guilt as if it were a form of devotion. You let love cost what it costs.”
Noah looked away, because the sentence had found the deepest thing immediately. For nearly a year he had believed his unrelenting misery was a kind of tribute to Caleb, or at least a debt correctly paid. If he suffered enough, remained joyless enough, withheld enough from himself and from his mother, then perhaps the universe would note that he had not moved lightly past the life he failed to save. But hearing it named that way now, he saw how self-centered the arrangement had become. His guilt had not raised Caleb. It had not comforted his mother. It had not made him truer. It had only kept him bowed over himself, mistaking self-punishment for love.
His mother leaned one elbow on the rail, as if the conversation had moved beyond her strength to stand without support. “If we go home today,” she said, “I want to hear the message.”
The fear came back all at once, quick and physical. He had listened to the voicemail maybe fifty times in eleven months, each time hoping the sound of Caleb’s voice would finally do something other than split him open. The thought of his mother hearing it felt unbearable.
“No.”
She turned to him. “No?”
“I can’t.” He shook his head too hard. “You don’t understand. It’s not just his voice. It’s how afraid he sounds. It’s how long I let it sit there. If I make you hear that too—”
“If you don’t,” she said, and now there was a firmness in her voice that reminded Noah she had once worked double shifts and still come home with enough authority to stop two teenage boys from turning the house into a disaster, “then you are still choosing for me what pain I’m allowed to carry. That is what you’ve been doing all year. You call it protection because the other name for it would make you stop.”
Noah stared at her. The sentence might have sounded harsh from someone else. From her it sounded exhausted, honest, and heartbreakingly clear.
The man beside them spoke quietly. “Truth does not only uncover what was wrong. It also returns choice to the people who were denied it.”
Noah thought of that night again, but not in the usual way. Usually he remembered the voicemail as the moment of his failure. Now, against his will, he began to see the year after it as its own long extension of the same choice. Caleb had asked for help and Noah had withheld himself. Then his mother had lived inside a fog of partial reality and Noah had withheld again, telling himself that one concealment justified the next because the original wound was too deep to expose. He had imagined himself fixed in place by grief. In truth he had been making the same fearful decision over and over: keep love at a distance whenever it asks something that might break you.
His mother unfolded her hand and held Caleb’s watch toward him. “Take it,” she said.
He hesitated, then took it. The metal was cold from the morning air. The leather strap had darkened with years of sweat and weather and whatever Caleb’s days had become toward the end. Noah turned it over once, seeing the small nick near the clasp where he and Caleb had dropped it on the driveway as teenagers trying to replace a battery with the wrong tools and too much confidence.
“He wore that the summer he worked with you on the crab boat,” she said.
“I remember.”
“He said you trusted him with real things out there.”
Noah looked down at the watch in his hand. “Sometimes.”
“No,” she said. “More than he thought he deserved. He told me that once.” Her voice softened. “You were not nothing to him because you failed him one night.”
Noah closed his fingers around the watch until the edges pressed into his palm. For months he had let one terrible decision rewrite every earlier chapter between him and Caleb. It had been easier, in a dark way, than holding the fuller story. If he was simply the brother who did not come, then the world remained brutal but simple. To admit he had loved Caleb imperfectly for years, and that Caleb had known it and depended on it anyway, was more frightening. Love made the loss larger. It also made the shame less absolute.
The man began to walk back toward the café. After a few steps He stopped and turned, not to command, only to invite.
“Come when you are ready,” He said. “There is still time before the day hardens.”
Noah watched Him go. His mother remained beside him, not touching him yet, not forcing closeness where truth had only just opened the door. They stood there a long moment, looking out over the harbor where the first clean brightness of morning had now taken hold of the water completely.
“I don’t know how to do this,” Noah said.
His mother gave a tired, sad smile. “Neither do I.” She tucked both hands into her coat pockets. “But for the first time in a long while, that doesn’t feel like the end of the sentence.”
Noah nodded slowly. The fear had not gone. If anything, it had become more concrete. It had a shape now: the drive home, the kitchen table, the phone set between them, Caleb’s voice filling the room neither of them had been able to enter honestly since he died. It would hurt. It would reorder things. He could not imagine coming through it unchanged.
And yet under the fear, something else had appeared, thin but unmistakable. Not relief. Not ease. Something more like the first sound of ice loosening on a river when winter has not fully ended but can no longer hold everything still.
He slipped Caleb’s watch into his jacket pocket and turned toward the café, where warm light still poured across the dock boards. His mother walked beside him, her steps slow but steady. Neither of them spoke. They did not need to. The morning itself seemed to know they were crossing from one kind of pain into another, and that the second kind, though no gentler at first touch, might finally lead somewhere the first never could.
Chapter Four
The drive home took twelve minutes if the lights on Harbor Road were kind, but that morning it felt longer because no one tried to shorten it with conversation. Noah drove with both hands fixed on the wheel, his mother beside him with Caleb’s watch no longer in her hand because it sat in Noah’s pocket now, a small hard weight against his leg. In the back seat, the man from the dock looked out the window as the town passed by in pale, ordinary pieces: the laundromat with one machine always broken, the mural of blue herons on the brick pharmacy wall, the shuttered gift shop with its summer postcards fading in the glass. He did not fill the silence. He did not turn the car into a chapel or a courtroom. He sat with them the way a person sits beside the wounded when words are not yet medicine.
Their house stood on a narrow lot three streets inland from the harbor, where the salt air still reached but the gulls were only background. It was a modest house with white siding that had yellowed in places, a porch swing Noah’s father had hung before his heart failed, and rosemary in two cracked clay pots by the steps because his mother said every house should smell like something living when the wind changed. Noah had not looked at the place carefully in months. He came and went through it the way people move through rooms where grief has settled into the furniture. That morning the house seemed to wait for them.
His mother unlocked the door and stepped inside first. The heat had been left low, and the air carried the faint mix of laundry soap, old wood, and the lemon oil she used on the dining table when she was anxious enough to clean. The hallway held framed photographs that Noah could usually pass without seeing. Now every one of them caught his eye. Caleb at eight with a striped towel tied like a cape around his neck. Caleb at fifteen holding up his first keeper redfish, proud enough to split his face open with a smile. Caleb at twenty-three at Thanksgiving, thinner than he should have been, already carrying a strain around the eyes, though Noah had not named it clearly then. There were photos of Noah too, of course, but grief had made the wall feel like Caleb’s corridor more than anyone else’s.
His mother took off her coat and hung it on the hook by the pantry. “Kitchen,” she said, not sharply, just naming what came next before either of them could wander into delay.
The man followed them in, moving through the house as though He belonged anywhere truth was about to cost something. Noah set his keys on the counter and stood for a moment looking at the table. It was square, scarred near one edge from a pan set down too hot years before, with one chair that wobbled if you leaned too far back in it. It was where they had eaten when Noah and Caleb were boys, where bills had been sorted, where apologies had started and failed and occasionally reached the other side. It was the table his mother had sat at after the funeral, hands around a mug gone cold, while neighbors filled the refrigerator with casseroles none of them really tasted. Noah had avoided being here with her any longer than necessary ever since.
His mother opened the kitchen drawer beside the stove and took out her phone. She looked at it for a moment before setting it face down near her plate as though making a small confession in advance. “I turned the sound back on months ago,” she said. “I don’t know whether that helps anything. I just wanted you to know.”
Noah nodded. He did not know what to do with the tenderness and pain of that sentence at the same time. The man pulled out the chair nearest the window but did not sit until Noah’s mother had taken her place. Noah sat last. The room beyond the kitchen window held the backyard garden in its winter-thinned state, rows of tired soil and cabbage leaves chewed by cold. At the fence line stood the old fig tree Caleb once fell out of and insisted he had meant to jump from. Noah remembered the blood on his lip, the dirt on his shirt, the way he laughed through pain when embarrassment was in the room.
His mother folded and unfolded a paper napkin with careful fingers. “Before we listen,” she said, “I want the whole truth about that night. Not the dramatic version. Not the shortest version either. I want what happened.”
Noah stared at the grain of the table. “I was home.”
She waited.
“I had just gotten in from the boat. It was late. I’d had two charters cancel that week because of the weather, and the engine was making that knocking sound again.” He rubbed the heel of his hand against his brow. “You had already gone to bed. I remember hearing the bathroom fan and the television through your wall. I had a sandwich on the counter. My phone rang while I was still wearing deck boots.”
He could see it now with brutal clarity, not because memory had improved but because he had rehearsed it so many times in secret. The kitchen light too bright over the sink. The stack of mail he had not opened. His own name on the charter company shirt, salt-stained across the chest as though someone more competent wore it. Caleb’s number lighting up the screen with the same old contact photo Noah had never changed, taken years before on a beach day when neither of them knew what was coming for the other.
“I let it ring because I knew it was him,” Noah said. “I knew from the hour. I knew from everything. I didn’t want to hear what he needed because I was already building my no before he even spoke.”
His mother’s mouth trembled once and steadied. “Then what?”
“He left the voicemail. I didn’t listen right away. I ate half the sandwich first.” Saying it aloud felt uglier than he had expected. “Then I listened.”
He stopped. The kitchen clock over the stove clicked forward one second, then another. From outside came the distant sound of a dog barking two houses down, and the soft rustle of branches scraping the fence.
His mother said nothing, but her eyes held him to the table.
“He sounded sober enough to know he was scared,” Noah said at last. “That was what made it worse. If he’d sounded drunk or high, I could have told myself I was hearing chaos again. But he sounded clear. Tired. Ashamed. He kept trying not to sound ashamed. He said they were releasing him and he didn’t trust himself walking. He said he’d wait outside under the awning if I came soon.” Noah swallowed. “Then he said, ‘Please don’t make me figure this out by myself tonight.’”
His mother put her fingers to her mouth and looked down at the table. Noah did not stop now. The truth, once moving, seemed to know how to find its own shape.
“I stood there listening to him breathe at the end. He didn’t hang up right away. I think he was hoping I’d answer after all and hear him live instead of recorded.” Noah shut his eyes briefly. “Then I replayed it. And replayed it again. I kept telling myself if I went, it would only continue what had already been happening for years. One pickup. One crisis. One promise. One collapse. I told myself someone at the center would see him there. I told myself he was a grown man and I couldn’t be his fence forever. I told myself ten things that all sounded wiser than what they really were.”
His mother lowered her hand from her face. “Which was?”
“I was tired of loving him when love felt like drowning.”
The sentence sat in the room and changed it. He could feel it, not because it was the worst thing he had said, but because it was the truest one. So much of his silence had been built on the fear that if people knew this, they would confuse exhaustion with absence of love. Perhaps he had confused it that way himself. But saying it now, with his mother across from him and the man by the window listening without flinching, he understood that the horror of that night was not that he had never loved Caleb. It was that love had become entangled with fear and fatigue until he had mistaken withdrawal for survival.
His mother let out a long, thin breath. “I know that feeling,” she said.
Noah looked up, startled.
She stared not at him but at the sink, where morning light had begun to stripe the dish rack. “Not the same moment. Not the same cost. But I know what it is to be so tired of trying to save someone that you start praying for silence instead of rescue. I know what it is to dread the sound of your own child’s voice because every conversation carries another edge.” She pressed the napkin flat against the table with her palm. “I hated myself for that every time.”
Noah had always thought his mother’s grief moved in a cleaner line than his own, because mothers were supposed to love without mixture and bear suffering without the grime of resentment. Hearing her speak now broke something false in him. She had not been standing on a high bright ledge above his failure. She had been stumbling through the same dark country with different wounds.
The man by the window finally spoke. “Love becomes distorted when people carry burdens they were never meant to carry alone. Then fear begins speaking in love’s name.”
His voice entered the kitchen softly, but it reached all the way back through years. Noah thought of Caleb at twenty-eight, sweating through withdrawals in the back bedroom while Noah changed the sheets and his mother stood at the sink crying quietly where she thought no one could hear. He thought of every promise Caleb made and meant for one hour or one week before the hunger returned stronger than intention. He thought of all the times Noah had told himself he was the last barrier between his brother and the grave, and how that belief had made him feel necessary right up until it made him cruel.
His mother looked toward the man. “If that’s true, what are we supposed to do with the fear after it has been speaking so long it sounds like your own thoughts?”
He met her gaze. “You tell the truth about it. You stop calling it wisdom when it is only terror with manners.”
The words would have sounded severe from someone trying to win an argument. From Him they felt like a blade used by a surgeon, sharp because infection had already run long.
Noah reached into his jacket and took out Caleb’s watch, setting it on the table between them. The scratched face caught the light from the window. He did not know why he did it exactly, only that it felt wrong to speak of Caleb as an event while his objects still lived in drawers and duffels and pockets. His mother touched the edge of the watch with one finger and then withdrew her hand as though it burned.
“The message is still there,” Noah said. “I kept it.”
His mother nodded once. “Play it.”
He took out his phone, and for a terrible moment his hands shook so much he could not unlock it. The man rose from His chair, came around the table, and rested one hand lightly against the back of Noah’s seat. It was a small thing, almost nothing. Yet the steadiness in it moved through Noah with a force that surprised him. He was not being held in place. He was being kept from slipping out of himself.
The voicemail sat where it had always sat, archived and starred as though organization could make it less haunted. Noah pressed play.
At first there was only the grainy hiss of bad signal and street noise in the background. Then Caleb’s voice came, tired and thinner than Noah remembered from life, though that might have been the recording. He said Noah’s name once casually, like a man calling from a grocery aisle. Then again with less cover in it. He explained where he was, mentioned the release, made a joke about the coffee there tasting like wet cardboard, and then the joke fell away because he did not have strength to keep pretending. He asked for a ride. He said he knew Noah was tired of this and that he did not blame him. He said he did not trust the part of himself that always got loud when he was alone too quickly. Then, near the end, came the line Noah had already repeated inwardly a thousand times and still could not hear without feeling something inside him split open: please don’t make me figure this out by myself tonight.
After that there were four seconds of breathing and then the soft mechanical click of the call ending.
No one moved.
His mother’s face had gone wet in complete silence. Not the dramatic weeping of films, just tears running down the skin as if something long frozen had finally begun to thaw without asking permission. Noah could not breathe normally. He had thought listening with her would multiply the wound. In one sense it did. But another thing happened too. The voice no longer belonged only to the chamber of his private punishment. It existed in the open now, terrible and human and shared.
His mother reached across the table, not toward the phone but toward Noah’s wrist. He let her take it.
“I am so sorry he was alone,” she said. “And I am so sorry you have been alone with this.”
The mercy of that nearly broke him more than accusation would have. He bent forward, both hands over his face, and for the first time since Caleb died the tears came without the hard inward resistance that had always made them feel like another form of self-attack. He cried as a grown man cries when dignity has finally lost the war against truth. His mother kept hold of his wrist. The man’s hand remained on the back of his chair. No one rushed him toward composure.
When he could finally sit upright again, the room looked altered, not because grief had lessened but because shame had lost its monopoly on it. His mother wiped her face with the heel of her hand and gave a small embarrassed laugh at the wet napkin destroyed between her fingers.
“Do you know what I keep thinking?” she said.
Noah shook his head.
“I keep thinking he sounded like himself.” She looked at the phone as if it were both a wound and a relic. “Not the version addiction carved out of him at the end. For a few seconds there, I heard my son ask for help the way he did when he was little and trying not to cry.”
Noah nodded, unable to answer.
The man returned to His seat. The kitchen had gone very quiet, but not empty. The kind of quiet now was different from the quiet that had ruled the house for months. That one had been full of avoidance, each person protecting the other by withholding what might undo them. This quiet held sorrow too, but it also held witness. The truth had been listened to, not merely dropped between them like a stone.
His mother looked at Noah for a long time. “There is something else,” she said. “If we are doing this honestly, then I need to tell you what I found in the hall closet besides the papers.”
He felt a small twist of dread, but not the old kind. This felt more like standing in a doorway knowing another room had yet to be entered.
“What?”
She rose, left the kitchen, and returned with a shoebox from the hall table. Inside were rubber-banded stacks of envelopes, some opened, some not, all addressed in Caleb’s rough uneven handwriting. Noah frowned.
“He wrote these?”
She nodded. “Off and on the last year. Some from treatment, some from before that, some with no stamp because I don’t think he ever meant to mail them. I only read one. It was to me. I stopped because it felt wrong to keep going alone.”
Noah looked from the box to her face. “Why didn’t you tell me?”
“Because I was afraid of what they might ask of us.” A tired smile touched her mouth and faded. “Apparently fear has had a room in this house for a while.”
The man by the window looked at the box and then at them. “You do not need to open everything today,” He said. “But you do need to stop building your life around unopened things.”
Noah felt the words settle deeply. The voicemail, the letters, the closet, the duffel on the boat, the words never spoken at the funeral, the kitchen table avoided except for bills and weather and small talk. His life had become architecture built around sealed rooms. He had told himself this was endurance. Perhaps it had only been delay with a heroic face.
His mother slid the shoebox onto the center of the table beside Caleb’s watch and Noah’s phone. Sunlight moved higher across the wood, touching all three objects at once as if the morning itself had decided not to let any of it stay in shadow.
“We won’t read them all now,” she said. “But tonight, after dinner, we read one. Tomorrow, maybe another.” She looked at Noah with a steadiness he had not seen in her since before the funeral. “And you’re not sleeping on that boat anymore. I’m done pretending distance is the same thing as strength.”
He almost argued out of reflex. Then he realized the argument would not be about logistics or pride. It would be about whether he was willing to return fully to a life where love could find him and ask more. He looked toward the man, and in that brief glance he felt again what he had felt on the dock: not pressure exactly, but an invitation so clean it left his evasions looking small.
“All right,” Noah said.
His mother nodded once, as though something practical had been decided, though both of them knew the decision reached further than where he would spend the night.
Noah looked down at the box of letters. “I don’t know if I can bear hearing his voice in a different form too.”
“You can,” the man said. “Not because you are strong enough to master it, but because love will stay with you inside it.”
Noah had no clever answer to that, so he let the sentence remain what it was. Outside, the neighborhood had fully woken. A mower started somewhere down the block. A child called to another child. The fig branches moved lightly against the fence in the salt wind. Everything ordinary continued, but the ordinariness no longer felt like mockery. It felt more like a promise that truth and daily bread had always belonged together, and perhaps healing would come that way too, not in one grand moment alone but at tables and in letters and through mornings honestly faced.
Chapter Five
By late afternoon the house had taken on the uneasy calm that follows deep honesty, when nothing looks different to a stranger and yet everything in the rooms has shifted a few inches from where it used to stand. Noah had changed out of his salt-stiff clothes and fixed the back gate latch his mother had asked about three times over the last month, not because the latch mattered much but because his hands needed work they could finish. His mother made soup from what was in the refrigerator and kept wiping the counter after she had already wiped it. The man moved quietly through the house as if He knew how to be present without becoming another task. Once Noah found Him in the living room standing before the wall of photographs, not studying them like a visitor, but looking at them with a kind of grief that felt closer than memory.
They did not read a letter at noon. Neither Noah nor his mother had the strength for that and for the voicemail both in the same day. Instead they ate in relative silence, then cleaned up together with the soft awkwardness of people re-learning one another’s company after months of skimming past the real things. Several times Noah caught himself wanting to disappear to the boat just for an hour, just to breathe diesel and salt and the old form of his life where every problem could be pushed farther out by water. Each time the desire came, he saw more clearly what it was. Not rest. Escape with a righteous face.
At four-thirty his phone rang.
He glanced at the screen and saw Pastor Glenn’s name. For a second the old habit rose again: ignore, delay, control the timing. But the whole day had been an argument against delay, so he answered.
“Hey,” Glenn said. “I was about to head over.”
“Why?”
A pause. “Your mom called me.”
Noah looked toward the kitchen, where she stood at the stove with her back to him, stirring the pot though the burner was off. She did not turn around. He could tell from the set of her shoulders that she knew exactly which call this was.
“What did she tell you?” Noah asked.
“That she and I need to stop protecting you from being known.” Glenn’s voice was gentle, but he had never been a man who hid firmness behind softness. “And that there’s a memorial service Sunday at the harbor chapel for families who’ve lost someone to overdose this past year. She wants Caleb named there.”
Noah shut his eyes briefly. The chapel sat three blocks from Slip Nine, a plain white building used for weddings in good weather and emergency prayer meetings in bad. He had avoided it since the funeral. “I’m not speaking.”
“I didn’t ask you to.”
“Good.”
Another pause. “She did.”
Noah opened his eyes and looked again at the kitchen. His mother had stopped stirring. The spoon rested against the side of the pot. The man sat at the table, hands folded, watching neither of them and somehow seeing all of it anyway.
“Why would she ask that?” Noah said, though he knew.
“Because the kind of truth you told today cannot stay private forever if it is going to heal anything beyond the two of you.” Glenn let that settle before continuing. “I’m not talking about public self-destruction, Noah. I’m talking about not spending the rest of your life acting like shame is a family value.”
Noah felt heat rise in him. “You don’t get to say that from your office with the little wooden cross and the tea kettle. You didn’t hear the message.”
“No,” Glenn said. “I didn’t. But I’ve buried enough people to know what silence does to the living.”
They ended the call without resolution. Noah set the phone down harder than he meant to and stood in the middle of the kitchen, anger surging up not only at Glenn, not only at his mother, but at the fact that truth had immediately begun demanding more truth. He had imagined confession as a terrible summit. Instead it seemed to be a door.
“I’m not doing it,” he said.
His mother finally turned. “I didn’t ask you to tell every detail.”
“You asked him to ask me to speak.”
“I asked him to tell you there will be a room where Caleb’s name is not whispered.”
Noah laughed once, short and sharp. “That’s not the same thing?”
“No.” She took off her apron and folded it over the back of a chair with careful hands. “One is exposure for its own sake. The other is refusing to keep your brother’s life and death inside this house as if secrecy were cleaner than sorrow.”
He looked to the man at the table, almost accusingly. “Are You with her too?”
“I am with the truth,” He said.
The answer stripped the room bare. Noah hated it because it refused team logic. This was not mother against son, pastor against fisherman, religion against avoidance. It was simply the next place obedience cost him.
He moved to the sink and braced both hands on the counter. Outside, the backyard had gone amber at the edges, the winter light lowering itself toward evening. He could hear a bicycle bell in the street, then the distant bark of the same dog as earlier, then the ordinary slam of someone’s truck door. The neighborhood was alive in all its plain ways while his chest tightened around the thought of standing in the harbor chapel saying anything with Caleb’s name in it.
“I can’t do it because I don’t trust my reasons,” he said at last. “If I speak, part of me will be trying to punish myself in public and call it honesty. Part of me will be trying to earn forgiveness by bleeding in front of witnesses.”
The man rose from the table and came to stand not beside him this time but across from him, on the other side of the narrow kitchen, where Noah had to meet His eyes to keep talking.
“That is why you do not go there to speak about yourself,” He said. “You go because your brother was more than his worst night, and because other people are drowning in the lie that hidden pain becomes holy if no one names it.”
Noah looked away first. The words found the place inside him still trying to make his guilt the center of every room. Even Caleb’s death had become, in Noah’s secret handling of it, another mirror angled back toward Noah’s failure. To speak at all would require lifting his eyes off himself long enough to bear witness to his brother as a person, not merely an accusation.
His mother lowered herself into the chair by the table, suddenly looking very tired. “I don’t need a polished speech,” she said. “I need one honest thing said aloud where silence has ruled too long.”
He rubbed a hand over his face. “And if I fall apart?”
She gave a small sad smile. “Then you fall apart in church, like generations before you.”
The faint humor in that undid some knot in him. Not enough to make the decision easy, only enough to make it human-sized again.
The man spoke more quietly. “You have spent eleven months believing your suffering was the truest thing you could offer your brother. It is not. Truth joined with love is truer.”
The room went still.
There it was again, the central wound exposed in a single sentence. Noah had not only believed he had failed Caleb. He had built a private religion around the idea that ongoing misery was the most faithful response left to him. Joy would betray. Rest would betray. Full belonging in his mother’s home would betray. Laughter, good food, honest sleep, light on the harbor, all of it had felt suspect because Caleb no longer had it. Noah saw now how that belief had hollowed him. It had given him no way to love the living except from a distance.
“I’ll read one letter first,” he said. “Before I decide anything about Sunday.”
His mother nodded. “All right.”
She brought the shoebox to the table. The envelopes inside had been tied in small stacks with the kind of rubber bands that leave marks on paper over time. Some bore dates. Some did not. One had his name on it in Caleb’s uneven hand: Noah. No joke, no nickname, no attempt to soften anything. Just his name.
His stomach tightened.
His mother touched the envelope and then withdrew her hand, leaving the decision to him. The man resumed His seat by the window, giving the table back to the family while still somehow holding the whole room in His quiet attention.
Noah opened the envelope carefully, though one corner still tore. Inside was a folded sheet from a legal pad, the blue lines faint where the pen had pressed too hard. Caleb’s handwriting lurched across the page in places, steadier in others. Noah began to read silently, but halfway through his mother said, “Read it out loud,” and he knew she was right.
His voice shook only on the first line.
If you’re reading this, it means one of two things. Either I finally got brave enough to hand it to you, or I didn’t and somebody else had to do what I kept not doing.
Noah stopped, swallowed, and continued.
I know I’ve made your life smaller. I know there were years when every time my number came up on your phone, your whole body probably got tired before you even answered. I know because I’ve seen your face when you tried not to show it. I’m not writing this to ask you to carry me forever. I think part of what ruined us was me confusing love with making you hold what I would not face.
The kitchen seemed to contract around the words. Noah felt each sentence land in places shame had long occupied alone.
I need you to hear this one clean: if I die, I do not want you turning my death into a room you live in. You always do that, No. You think guilt is loyalty if you wear it long enough. It isn’t. It just makes you absent while you’re still breathing.
Noah could not read for several seconds. His mother reached for the salt cellar and gripped it instead of his hand, perhaps because she needed something solid and small enough to bear.
He kept going.
You loved me more than I knew how to hold. I knew that even when I was mad at you. Especially then. If I ever get clear enough to become a different man, part of it will be because somebody kept telling me I was more than the mess. If I don’t get clear enough, that still stays true. Don’t let Mom sit alone in that house and don’t punish yourself in my name. It would be the dumbest monument anybody ever built.
There was one more line, crooked and squeezed at the bottom of the page.
Also if you sell the boat, I will come back and haunt you in ways you deserve.
Noah let out a sound that was half-laugh, half-sob, and his mother covered her mouth as tears spilled again. For a moment Caleb was in the room not as an emergency, not as a corpse, not as the last voicemail, but as himself: rough, observant, darkly funny, more loving than either of them had trusted he still knew how to be.
Noah lowered the page. The whole kitchen had gone luminous with evening now, the window throwing a thin gold across the table that touched the letter, the watch, the box, his mother’s wet face, the hands he could not make stop trembling.
“He knew,” Noah said softly.
His mother nodded. “Yes.”
“He knew me.”
“Yes.”
All year Noah had lived inside the assumption that the truest version of Caleb’s final knowledge of him was abandonment. The letter did not erase that night. Nothing could. But it shattered the lie that one decision had become the only thing Caleb saw. Caleb had known Noah’s fear and exhaustion, and still named his love without flattery. More than that, he had recognized the exact trap Noah would build afterward. It was as though his brother had reached ahead through the dark to warn him about the shape grief would take if left unguided.
The man by the window spoke at last. “Now you know what costly obedience is.”
Noah looked toward Him.
“It is not merely admitting what was done,” He said. “It is refusing to keep building your life around the wound once truth has opened a way through it.”
The sentence settled like a bell in the room.
Noah looked at his mother. “If I speak Sunday, I won’t tell everything.”
“You shouldn’t.”
“I won’t make it about how guilty I feel.”
“Good.”
He drew a long breath. “I’ll say his name. I’ll say he asked for help. I’ll say silence nearly buried the living with the dead.”
His mother’s eyes filled again, but her mouth steadied into something firmer than grief alone. “That would be enough.”
Noah folded the letter and placed it back in the envelope, though not back in the box. He kept it near his plate. For the first time since Caleb died, he did not feel as though remembering his brother required him to lock himself inside pain. The pain remained, deep and undiminished. But another current moved beneath it now, one Caleb himself had named: love not ending at the wound.
Outside, the sky had gone the color of worn copper above the fence line. Noah stood and went to the back door. He opened it and let the evening air into the kitchen. Rosemary, cold dirt, salt from the harbor. The whole world smelled alive and unfinished.
Behind him he heard the slight movement of chair legs. When he turned, the man was standing again, ready in the quiet way He always was, as though each next thing had already been held in prayer before it happened.
Noah put one hand on the doorframe and looked at Him. “I’ll do it,” he said.
The man’s face did not brighten with triumph. He only held Noah’s gaze with that same unshakable mercy and truth that had met him on the dock before daylight. “Then let tomorrow teach your feet what your heart has begun to learn.”
Noah did not fully understand the sentence, but he knew enough. Sunday would not be performance. It would be walking into a room he had avoided and telling one honest thing where people could hear it and not turn away. It would be love costing pride, costing privacy, costing the old familiar bond with self-punishment. It would be small by public standards. In heaven, Noah suspected, it might be called large.
Chapter Six
Sunday came with a thin gray sky and the kind of cold that made the harbor smell cleaner than usual, as if the wind had scraped the air down to metal and salt. Noah woke before dawn in his old bedroom at the back of the house, not because he had slept well, but because his body still had not learned that truth told aloud might let a man rest differently. For a few seconds he did not remember where he was. Then he heard the faint rattle of the heat vent, the porch swing tapping once against its chain outside, and the low murmur of a voice from somewhere deeper in the house.
He got up quietly and followed the sound. The living room was dark except for the small lamp by the sofa. Jesus was there alone, kneeling beside the chair near the front window where Noah’s father used to read the paper before work. His hands were folded, His head bowed, and there was no strain in His stillness, no trace of performance. He was simply with the Father, present in a way that made the room feel more solid than wood and plaster should have. Noah did not interrupt. He stood in the hallway and watched for a moment, not as a spy on something private, but as a man seeing again the source of the steadiness that had held him all week.
When Jesus lifted His head, He did not look surprised to find Noah there.
“You’re awake,” He said.
“No sleep worth bragging about.”
Jesus rose. “Truth seldom makes the first nights easier. It makes them real.”
Noah leaned against the doorway. “I’ve been trying to decide whether I’m more afraid of speaking or of what happens after I speak.”
Jesus came toward him with the calm of someone who did not need to reduce fear in order to master it. “What happens after is that you keep living,” He said. “But not inside the same lie.”
The sentence stayed with Noah while he dressed, while he drank the coffee his mother had already made, while the two of them rode in near silence toward the harbor chapel. She wore the green coat again, with a navy scarf tucked close around her neck. Noah wore the only dark jacket he owned that did not smell like bait or fuel. The letter Caleb wrote lay folded in his inside pocket, not because he planned to read it, but because he needed to know it was there. The watch was on his wrist. It fit loosely. Caleb’s wrists had always been thinner.
The harbor chapel stood where it always had, plain and white with salt staining the lower boards and a small wooden cross mounted above the door. It was not large enough for grandeur. That had always been part of its mercy. It held fishermen’s funerals, storm prayer meetings, two weddings Noah could remember, and once a blessing service for a family whose house had burned down. Inside, the pews were simple pine, the windows narrow, the heat uneven. The room smelled faintly of old hymnals, wet coats, and candle wax.
People were already gathering when Noah and his mother arrived. He recognized faces from town, some he had not looked directly at in months. Mrs. Alvarez stood near the back in a burgundy sweater, speaking softly with a woman whose son had died in July. Pastor Glenn met Noah at the door, not with the anxious grin he sometimes used when bracing for difficult conversations, but with a grave, quiet nod.
“You don’t owe anyone a performance,” Glenn said.
Noah almost answered with something defensive out of habit, then let the habit pass. “I know.”
Glenn glanced toward the front of the chapel. “That’s already more than you knew a week ago.”
The room filled in slowly. Noah sat with his mother in the third pew from the front. Jesus sat beside them for a few moments, then rose before the service began and moved toward the side aisle, where the shadows from the narrow windows lay cool and blue against the floorboards. Noah could still see Him there, but He had given the center of the room back to the people who needed to stand in it.
The service itself was gentle and unadorned. Glenn read a Psalm. A woman Noah barely knew wept through a memory of her brother teaching her to ride a bicycle. A father in a mechanic’s jacket stood at the lectern and could not finish more than three sentences about his daughter before grief closed his throat. No one hurried him. The room understood pauses. That too felt like mercy.
By the time Glenn spoke Caleb’s name, Noah could feel his own heartbeat in his wrists.
He had told himself all morning that he could still decline when the moment came. Glenn would understand. His mother would survive it. The truth had already been told in the kitchen, and perhaps that should be enough. Yet when Glenn turned from the lectern and looked at him, not summoning, only allowing, Noah knew he had reached the place where obedience stopped feeling theoretical.
He stood.
The walk from the pew to the lectern was no more than twenty feet, but he felt each board under his shoes. He became aware of everything at once: the cough of an older man in the back, the squeak of one pew shifting as someone leaned forward, the scratch of his jacket sleeve against the wood. He was not a man used to speaking indoors where grief was listening. He knew how to shout above engine noise, how to tell customers where to sit on the boat, how to swear at rusted bolts and laugh too hard at harbor jokes. This was different. Here words had to stand without volume.
He reached the lectern and placed both hands on either side of it. The wood was worn smooth where other grieving people had done the same.
“My brother’s name was Caleb Mercer,” he said, and at first his voice sounded to him like it belonged to someone else. Then it steadied. “Some of you knew him from when he was younger. Some of you knew him later, when life had already become harder than he knew how to carry. Some of you only know the way he died.”
He looked down for a moment, not to avoid the room but to gather one honest thing from the place inside him where it had been hiding too long.
“I need to say aloud that the last truth is not always the whole truth,” he continued. “My brother struggled. He hurt people. He frightened people. He wore out the ones who loved him. All of that is true. But it is also true that he was funny in a dark room, and gentle with animals, and better with children than anybody would have expected if they only met him near the end. It is true that he used to wake me up before dawn just to drag me to the pier because he said the water told the truth before people started lying about themselves. It is true that he could still sound like himself when he asked for help.”
The chapel had gone very still. Noah felt the old instinct rise in him, the one that wanted to pull back before the next sentence cost too much. But he had not come here to protect himself from what love required.
“When Caleb died,” he said, “I told myself silence was respect. I told myself if I carried enough guilt quietly enough, that would prove I hadn’t taken his life lightly. What I’ve learned is that silence can become another way of leaving people alone.”
His mother sat very straight in the pew, her hands folded tight over her scarf. Jesus stood in the side aisle, unshaken, listening as though no word spoken truthfully in sorrow was ever small.
“My brother asked for help on the last night of his life,” Noah said. “And I did not come.” The words landed in the room with no drama around them, only weight. “I say that here not because this service is about me. It isn’t. I say it because hidden pain keeps wounding the living. I say it because families like ours learn how to survive by saying less and less until nothing honest can breathe in the house. I say it because people who are drowning need more than our private grief after they are gone. They need truth while there is still time.”
He paused. No one moved.
“I can’t change the night my brother died,” he said. “But I can refuse to build the rest of my life around that night alone. Caleb was more than the worst thing he did, and he was more than the worst thing I did. I loved him badly sometimes. I loved him tired. I loved him afraid. But I loved him. And I don’t think honoring him means disappearing into shame in his name. I think it means telling the truth and staying with the living.”
Noah’s throat tightened. He looked down once at his wrist and saw Caleb’s watch there, catching the dim light from the chapel windows.
“If anyone here has mistaken secrecy for strength,” he said more softly, “or guilt for loyalty, I hope you stop before it takes more from you than grief already has. That’s all.”
He stepped back from the lectern before his voice could fail him.
No one applauded. Noah was thankful for that. The chapel knew better. What came instead was quieter and somehow harder to bear. A woman in the second pew covered her face and wept. The mechanic who had spoken earlier lowered his head. Mrs. Alvarez sat with both hands pressed together under her chin, tears on her cheeks and no embarrassment about them. Glenn returned to the lectern only after giving the room time to receive what had been said without rushing to translate it into lesson or closure.
When Noah sat down again, his mother reached for his hand and held it tightly enough to hurt. He let it hurt. Beside pain honestly borne, the small pain of her grip felt like belonging.
The rest of the service passed in a blur of prayer and names and the low creak of pews as people stood and sat. By the time it ended, the gray sky had broken open and a thin white light had begun to spread across the harbor. People lingered outside the chapel afterward in the cold, speaking quietly, some to one another, some to Noah, some to his mother. Not all the words were useful. Grief rarely produces only useful words. But something had shifted. The secrecy around Caleb’s life and death no longer felt like a sealed tomb only the Mercer house could enter. The truth had gone public in a clean enough way that other wounded people could step near it without being crushed.
A man Noah barely knew from the fuel dock touched his shoulder before leaving. “My brother called me once and I didn’t answer either,” he said, then shook his head as though no more language would improve the honesty of that. He walked away with tears in his eyes. A teenage girl stood with her aunt near the chapel steps and would not stop looking at Noah, not in accusation, but in the startled way people look when they hear a hidden thing named and realize it has been living near them too.
By early afternoon the crowd had thinned. His mother had gone with Mrs. Alvarez to the café for soup, promising Noah she would save him some. Glenn was speaking with the family from July near the parking lot. Noah found himself alone on the harbor path with Jesus, the wind moving hard enough off the water to redden his cheeks.
For a while they walked without speaking. Boats knocked softly against their bumpers. Ropes strained and relaxed. The whole marina seemed caught between season and season, not empty, not full, waiting for the busier months while still faithful to the work of this one.
“I thought I’d feel lighter,” Noah said at last.
Jesus looked out over the water. “Do you?”
“No.” He considered. “Not lighter. Just less divided.”
Jesus nodded, as if the distinction mattered. “That is often how healing first arrives.”
They stopped near Slip Nine. Noah’s boat rode there in the afternoon chop, no more beautiful than before, but no longer looking like an exile either. The blue duffel still sat inside the cabin where Noah had left it months ago. He looked at it and knew at once what the next obedience would be. Not to throw it away. Not to keep it untouched forever. To bring it home and go through it with his mother when they were able. Another unopened room, smaller now that truth had already entered the house.
“I’m still going to miss him in all the places,” Noah said.
“Yes.”
“I’m still going to hate that I didn’t go.”
“Yes.”
Noah exhaled into the salt air. “Then what changes?”
Jesus turned toward him, and in His face Noah saw the same holy steadiness that had met him on the dock before dawn days earlier, before the kitchen table, before the letters, before the chapel. “The wound no longer gets to tell the whole story,” He said. “Love tells it with the wound now. Truth tells it with the grief. And you remain among the living.”
The harbor path ended at the breakwater, where the morning of the first day had begun. They walked there together. The light had gone clearer by then, laying silver over the water until the channels between the boats shone like opened seams. Jesus stepped out to the far end of the stones and grew quiet. Noah did not ask another question. Some answers were already larger than his understanding and would have to be lived before they could be fully known.
He stood back and watched as Jesus bowed His head and began to pray.
The wind pressed against His coat. The gulls wheeled above the slips. Behind them the harbor town kept moving in all its ordinary needs: lunches served, engines repaired, children called home before dark, letters waiting in boxes, griefs carried from room to room until truth made another way. Noah stood within that living world and felt, not the end of sorrow, but the strange steady beginning of hope inside it. The city, the harbor, the house, the dead, the living, all of it was being seen by God.
And for the first time in a very long while, Noah did not turn away from being seen too.
Your friend, Douglas Vandergraph
Watch Douglas Vandergraph inspiring faith-based videos on YouTube: https://www.youtube.com/@douglasvandergraph
Support the continued growth of the Douglas Vandergraph Christian encouragement library: https://www.buymeacoffee.com/douglasvandergraph
Tuesday
from  Roscoe's Story
Roscoe's Story
In Summary: * Most notable thing about this Tuesday was doing my Monday laundry. Didn't get to it yesterday as I spent most of the morning preparing for the midday meeting at my bank, which went well, I'm happy to say. So I took care of it today. It always feels good to have the weekly laundry all done, folded, and put away, ya' know?
Nothing ahead of me now but a good relaxing foot soak, then the night prayers, then an early bedtime.
Prayers, etc.: * I have a daily prayer regimen I try to follow throughout the day from early morning, as soon as I roll out of bed, until head hits pillow at night.
Health Metrics: * bw= 235.9 lbs. * bp= 154/88 (67)
Exercise: * morning stretches, balance exercises, kegel pelvic floor exercises, half squats, calf raises, wall push-ups, BP breathing exercises
Diet: * 05:36 – 1 banana * 06:40 – 1 pb&j sandwich * 09:00 – beef patties, mashed potatoes, mushroom gravy * 14:00 – sauteed bitter melon, little sausages, steamed white rice * 16:20 – 1 fresh apple
Activities, Chores, etc.: * 04:00 – listen to local news talk radio * 05:00 – bank accounts activity monitored. * 05:15 – read, write, pray, follow news reports from various sources, surf the socials, nap * 08:00 – start my weekly laundry * 10:40 – listen to curent John Michael Chambers reports while folding laundry * 13:00 – watching MLB Central on MLB Network * 14:00 – watching old episodes of Stargate SG 1 on Comet TV * 16:00 – following news reports from various sources, surf the socials * 17:00 – listening to relaxing music
Chess: * 10:25 – moved in all pending CC games
from  Jon Kalev
Jon Kalev

Caption text here



from  Jon Kalev
Jon Kalev



I ought to do something about my posture
from  The happy place
The happy place
I had an allergic fit yesterday, causing an intense headache which some people would think hurt a lot, I thought to myself
So I went to sleep; I slept the whole day and it didn’t go away, so I slept the whole night too
Woke up next day at 08:00 feeling tired, really exhausted, isn’t that odd? Must’ve slept 16 hours? Or more? But, there was no headache
I really appreciate the absence of headache
And the sun shining down on me from up above through the foliage on this walkway where I walk facing the breeze
Walk with feet planted broadly like some sort of cowboy
Or sheriff
this world makes absolutely no sense to me.
The older I get, the less I know
absorption 003 - scattered likings
from  Semantic Distance
Semantic Distance
speaking terms / heat wave — snail mail
i into started listening to lush because i wanted to post a spotify link of my favorite song on twitter, all in attempts to get a like from a hot guy i (briefly) met at a house party. that aside, these two songs are some of the best indie rock to come out in recent memory. i’m most impressed with jordan’s guitar playing, switching between pretty abrasive strumming patterns and intricate finger plucking seamlessly. these songs also pair narratively: speaking terms seems to have the narrator assert their agency over an unloving partner insisting that they have unknowingly gone too far. despite this, heat wave starts with (presumably) the same speaker, waking up in their clothes having dreamt of them. we also can’t forget:
and i hope whoever it is holds their breath around you 'cause i know i did
on an oddly specific personal note, this song represents expansion. i remember looping this album as it accompanied me walking in between classes my freshman year of college. how crazy was it to be free for the first time?
detour / need for speed / basketball — kim petras
she needed a win so bad that she pulled out an unreleased sophie demo… this shit means something to her!!! no but seriously, i was really impressed with this album in an unexpected way. granted, i’ve been off kim petras since feed the beast came out with lackluster reviews, all of which she probably agrees with given her intentional (and 100% initiated) move away from massive record labels that have stifled her creative vision. even before that… wasn’t there an n-word scandal brought up by old tweets?
aside: i think we forget that miss petras was at the center of hyperpop before its transitional period to becoming that much more mainstream. this was back when charli xcx was signing douches at meet and greets after concerts and every self-proclaimed Twitter Gay was sending mine by slayyyter to all of his mutuals.
anyway… i’m glad she was able to independently create this project with a series of top notch producers like frost children and margo xs given that classic bubblegum pop sound with bright synths and opaque percussion was flattened by previous collaborators in her record label projects.
funny — broncho
i listened to this song when the weather just started to get warm in toronto after what felt like an eternal winter. spring was totally eclipsed by subpar temperatures and the need to put on a sweater every time you left the house in early may—basically an attack on my entire bloodline who lived in dewey temperatures for most of the year. ryan lindsey’s lyrics washed over me as the sun hit my skin not as a relief from cold but a reminder of warmth re: take a moment / for a moment / and i liked it.
the feeling — steve lacy
his voice has persisted throughout his progression as an artist. even if the production value increases, the writing remains honest and unique to lacy. i’m often wondering if the narrators in his songs are aware of their ego. in the feeling, he asks if he’s still cared for (am i your baby?) and states an eagerness to rekindle a toxic relationship (i’m not scared to bleed, you know our history).

the video for this song reminds me a lot of what he did for playground—a dreamy sequence of scattered, colorful visuals punctuated with lacy singing to the camera right in the foreground. he needs to keep kathleen heffernan on his production team ALWAYS!
Stay out of the digital oatmeal
from dsuurlant
Have you ever had a tension headache? Or a study, thinking headache? That tired feeling in your brain after doing a lot of learning — probably you felt it during your highschool exams and college thesis times, probably you felt it when you were trying to learn something new and really struggling. That’s because… learning things isn’t easy. Your brain has to do a lot of work, running through existing connections and building new ones. Over the course of my career as a software developer I became aware that the more I felt I was struggling, the more I was probably learning. It was only weeks or months after the fact that I could reflect and conclude, “oh, I was having a tough time because I was doing something new — and here’s what I learned”.
Learning thing is hard actually
I once experienced this most dramatically when things ‘clicked’ for me in Object-Oriented Programming. I’d been bashing my head against code for months. My approach was to just copy code from examples and tutorials, assert that it works (through mostly manual tests at the time — we’re talking 2003 – 2005 after all), and mumbling to myself “I don’t know why this works but it does”. I learned that in order to understand something, I first needed to put up with the frustration of not understanding it.
Now, everyone learns in different ways. Some people do great by just absorbing an entire manual and then know everything that was in it. Some people do best when watching videos, or having a teacher/mentor explain it to them. Me, I learn best through imitation, followed by examining what I just copied. “I built something that worked, because I did it like this — but why does that work?” Rather than making sure I get it all perfect and understand it perfectly before I build anything, I learn by doing and then reflecting on what I did. (I daresay I’m not unique in this and in fact most developers learn like this, which is why they’re great developers.)
I remember quite vividly the first time I typed something in Java like Button button = new Button(); At that point, I didn’t know what a class was, or an instance, or an object. I just knew I typed four words and three of those were the same word and I thought that was really funny. And that amusement spiked my curiosity and so I learned what those words meant in that context.
Why am I saying all this? Because obviously, nobody wants to learn anymore.
I think with the advent of AI everything, we’ve kind of forgotten that learning things is inherently taxing, frustrating, difficult, time-consuming, and just like, annoying to do. It burns energy, it gives you a headache, it might even make you feel bad about yourself. Because that’s what learning feels like! You don’t start at A and then magically, frictionlessly, arrive at Z. You gotta walk the steps.
But AI allows us to skip many of those steps. It has the capacity to think so you don’t have to, then give you the bullet-list, bolded-keywords, easily-readable version. But in my previously established pattern of learning, if AI writes the code for me, and I then review it by asking about what it just wrote, maybe I’m still learning, though? Maybe… maybe not.
Because I also distinctly remember typing over the example was much more effective than copy-pasting. In a similar vein, if you really want to commit something to your brain, write it down with your own hand. Physically. On paper.
There’s increasing amounts of research pointing to how increased use of LLMs decreases your brain’s capacity to think critically and learn things on its own. “Dumber” or “stupider” is quite a incendiary label, and I prefer to be a bit more precise about it, but the accumulation of cognitive debt is a real thing. And that’s because of the alphabet-journey I described earlier. If you’re skipping steps, you may get there faster, easier; but you simply won’t have picked up the learning along the way (the ‘debt’ the research points to).
Now think about how much time and effort you’ve spent during about the first 20 years of your life in education. School was hard work. Homework sucked. Studying for exams and taking them was so tough you might still have dreams about it. Writing your thesis, pretty much one of the toughest things you ever did cognitively, at least, up until that point. This is not to overvalue traditional education (there are plenty other ways to learn – on the job, self-taught, and so on). But my point is, none of that was easy. Your brain was working hard.
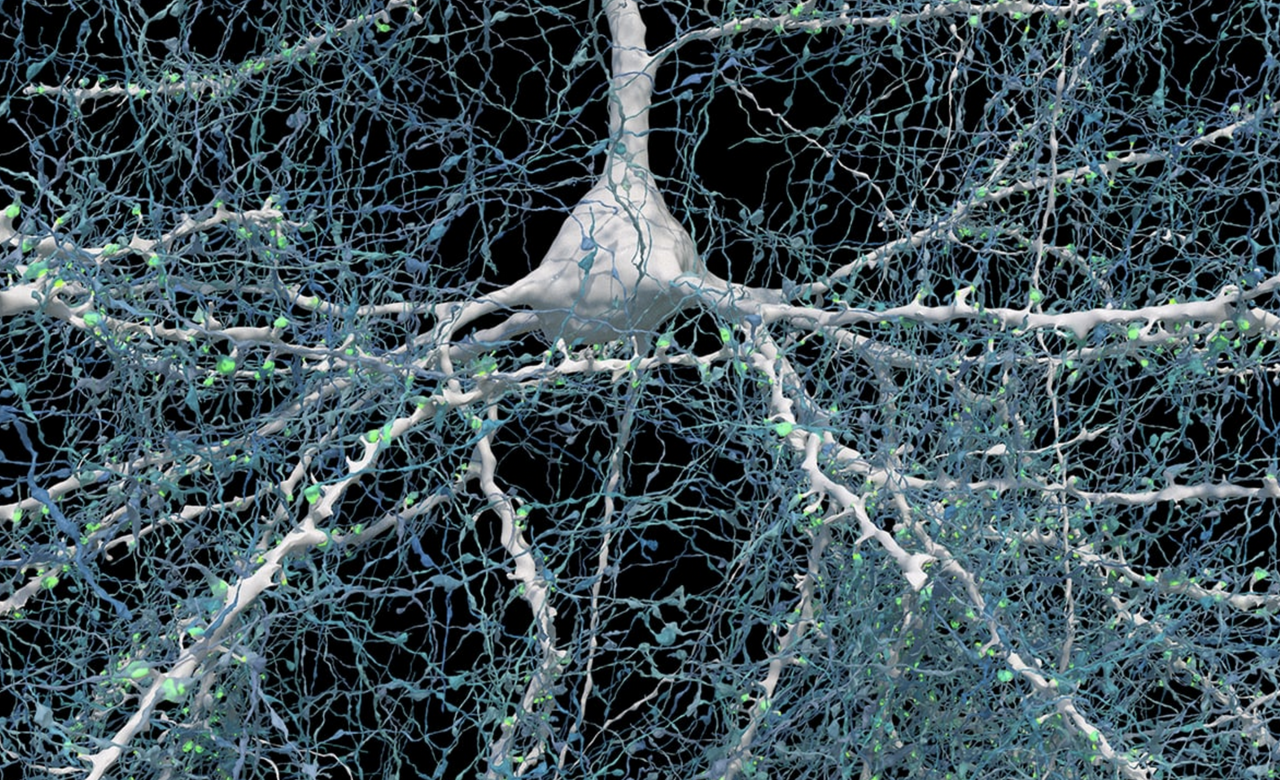
And it’s beautiful. (Source: Unseen details of human brain structure revealed, Google Research & Lichtman Lab, Harvard University. Renderings by D. Berger, Harvard)
I’ve been thinking about this a lot because I had a period last year where I was using LLMs quite intensively. I didn’t feel like I was getting dumber at the time, but that’s the thing, if I was then how would I know? This is the cognitive pitfall – if you are truly losing your cognitive thinking skills then you won’t be able to entirely catch and prevent that from happening. That’s what alarmed me. I was like, “well, I think I’m critically reviewing this thing’s output and still using my own thoughts and judgment but if I wasn’t then how could I be sure?”
The answer maybe is “if you’re at least still questioning that, then you’re good”. At the very least, it’s probably better to doubt yourself, than to just assume whatever the LLM responds with is always correct. If you’re not verifying the output in any way, then you’ve probably already been led astray and you’re not even aware of it…
Anyway, I’ve only been talking about learning so far, but there’s another aspect to this I want to bring up: creation.
Creating things is also not easy, turns out
Just like learning, making things is hard. Truly sitting down and making something out of nothing with your own mind and body is difficult, time-consuming, exhausting, challenging… and you often have to do it a lot, and deliberately, to even have it turn out kinda decent. This was humanity’s shared truth for a long time. Even when things came along that made creation more convenient, it still wasn’t easy. It required real cognitive effort. It’s why professional artists, musicians, writers, will often struggle with a creative ‘block’ where they just can’t synthesize something new; because it’s just that hard sometimes. Especially if they’re faced with their own perfectionism: knowing from talent or expertise what they want the result to be, and then not being able to get there.
The process of creation, and the process of learning, are very similar. When you make something, you are learning, and like me in order to learn anything you often have to go through the process of creation. An obvious example is knitting: you can’t learn how to knit by just watching videos. Your hands have to actually make something. A scarf, a beanie, a blanket. You make mistakes along the way, and you learn, and your knitting improves. You make less mistakes. Your stitches are more uniform. You knit faster.
AI makes it trivial to make something out of nothing. Using only a prompt, you can generate entire essays, songs, graphics, animations. I wonder if it’s because historically we’re used to creation being hard, thus valuable, that we haven’t adjusted to this reality where creation is easy, but we still value it as if it cost a real person blood, sweat and tears — when in fact it just cost you tokens. Because I’m curious and want to understand things I actually played around with these generators, and I found that the quantity is huge and the quality is just… not there. Certainly not the specific quality that I appreciate in any creation, which is the human quality.
I mean, you’re reading a blog post where every word was typed by me (yes, really!) I’m the woman who burst into tears the first time I saw The Sunflowers by Van Gogh and The Water Lilies by Monet. Real, human-made art affects me deeply, and I’m kind of hyper-sensitive to any creation that doesn’t have it.
That’s why over the past months I’ve grown increasingly frustrated and exhausted and annoyed with the AI slop that is just… everywhere. You see, I don’t necessarily mind if things are made with the help of AI (‘help’ doing a lot of heavy lifting in that phrase) Like, I get it, especially in a corporate context. We want more profit faster and what better way to get it than with automation instead of slower more expensive humans? (Although by now it seems humans are the cheaper option.)
What just truly grates me is the bad quality of it. Hands with too many fingers, graphs that are melting, words that are mangled, eyes that just aren’t quite right. Every blog post and LinkedIn post that now just reads the exact same effing way (which is why I am adamant about typing every word here, and if it still ‘sounds like’ LLM-speak that’s because I have unfortunately been influenced by reading and using it too much). Every single time I read “That’s not X, that’s Y” or a bullet-point list with sentences that don’t really say anything. UX designs that all look the same. Video thumbnails that all look the same. Everything is just the same, uninspired, AI-generated sludge. And it sucks, and it’s boring, and it’s just a waste of time to read/watch and a waste of resources to generate.
We can do better. Even if you want to generate things to get a headstart or whatever, you can still use your own judgment, add your own flavor. Hell, if you’re adamant about generating all your social posts at least teach the LLM to write like you so it’s not the same as every post out there nowadays.
Humans are imperfect, so everything we make ourselves is imperfect, which is exactly what makes anything interesting. I love reading something that’s clearly written in someone’s own voice and style. I love listening to music and seeing visual art where I can tell it has the maker’s characteristics there. Not everything has to be smoothed over. More importantly, if everything that’s created is the same, then why even do it? What’s the added value if it’s not expressing who we are and what our own story is? Am I the only one deeply annoyed by how samey everything is getting? (That’s separate from every other criticism leveraged against AI, mind you.)
The real kicker is, as I said, I’m not fully opposed to it. But what I see happening is that the “actual helpful use cases” are blurring together with “garbage output”, probably exactly because using LLMs intensively decreases your critical thinking skills. In other words, you might start out using it critically for specific applications, and end up not being able to distinguish quality stock photography from melting architecture and polydactyl people. You stop seeing what the big issue is. Endless LinkedIn posts full of “That’s not X. That’s Y” don’t even bother you anymore. You’re deep into the slop pool and the feeling of everything being that same gooey AI texture starts to be comfortable, like your mind sinking into digital oatmeal.
I’m not comfortable, here. I keep trying to use AI tools in meaningful ways, but I can’t do that and also tolerate all expressions of human creation and communication turning into grey goop.
There is real, measureable, significant value in the things we make ourselves and in the process of learning and creation, exactly because it’s hard. So go out there and make something yourself today! It’s worth the effort.
Because effort isn’t the enemy. Every blog post written like this is.
Especially if it ends like this—hitting hard.
With lots of periods.
And em-dashes.
HELP MAKE IT STOP NOOOooo—
from  Roscoe's Quick Notes
Roscoe's Quick Notes
Hoodies
from Tuesdays in Autumn
Among YouTube's better suggestions was to start showing me – around three or four years ago – home-made videos by the New York-based trio New Jazz Underground: this one, for example. For some time thereafter I kept up with their activity on Bandcamp, hoping for some of their music to appear on CD or vinyl. More time passed and eventually I stopped looking. By happy coincidence though, just last week something else on YouTube alerted me to the recent arrival of the trio's debut album Hoodies. A copy arrived here on Friday.
It's great to finally hear them playing in a studio setting, where their talent & technique shines, with no loss of the soulfulness & spontaneous charm that was obvious in their YouTube days. Most of the compositions on the album are by bassist Sebastian Rios, and he performs solo on one of the tracks – the marvellous ‘Las Salinas (Prelude)’. Saxophonist Abdias Armenteros demonstrates a clear and beautiful tone — not to mention a fine singing voice, which we hear on two songs. Drummer TJ Reddick meanwhile demonstrates equal facility with metronomic grooves and more elastic time-keeping. It’s a highly enjoyable record.
Another week, another old anthology of translated poetry, this one German Poetry 1910-1975, edited and translated by the estimable Michael Hamburger. It's a successor volume to an earlier one (Modern German Poetry 1910-1960) that he had co-edited with Christopher Middleton. In his introduction, Hamburger writes that, in place of the ill-defined notion of ‘modernity’, he substituted “a criterion quite as vague in itself, but meaningful as soon as it is applied to specific poems, specific poets: the criterion of authenticity, an authenticity usually bound up with novelty of one kind or another...”
I was already at least slightly familiar with the work of a number of the poets included (Rilke, Trakl, Brecht, Huchel, Bobrowski, Celan, Bachmann & Enzensberger). Among those whose names were new to me a couple that stood out were Yvan Goll and Ernst Meister. Also very interesting were the poems by authors better known for their prose: Robert Walser, Thomas Bernhard, Günter Grass & Peter Handke. The book is organised chronologically by the poets’ year or birth, which works well up until the end, where a variety of the youngest authors (perhaps then still not well-established names) are represented a little unsatisfactorily by a page or two apiece.
Cheese of the week – Baron Bigod, which must be up there among the best of English cheeses, akin to a very good Brie de Meaux. From the Fen Farm Dairy website: “Beneath the nutty, mushroomy rind, Baron Bigod has a smooth, silky golden breakdown which will often ooze out over a delicate, fresh and citrussy centre.” I first tasted it a few years ago, since when I've returned to it several times, finding it reliably excellent. I bought a ‘Baby’ 250g cheese (Fig. 26) from the Town Gate Butcher's shop in Chepstow on Saturday.
Herbal Resources
from Better Health Through a Better Mind

Photo by AS Photography from Pexels: https://www.pexels.com/photo/purple-petaled-flowers-in-mortar-and-pestle-105028/
